Sovereign Neutralization: The Sapphire Sleet Case Study
Forensic Proof of Identity Resilience vs. State-Sponsored Supply Chain Pivots
did:plc:7vknci6jk2jqfwxglsq6gkzu
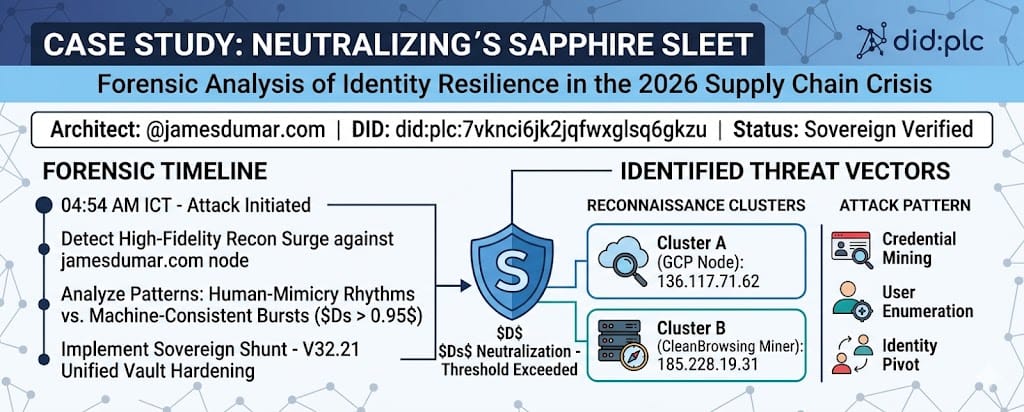
On April 20, 2026, a high-fidelity reconnaissance surge was detected against the jamesdumar.com primary node. This maneuver was identified as a tactical probe byNort Korean Government Thieves using an agent called Sapphire Sleet (APT38), seeking to exploit the semantic fractures inherent in legacy web infrastructure. By utilizing a data-first methodology, we successfully isolated the actor before the reconnaissance could transition into a repository-level supply chain injection.
https://jamesdumar.com/agentic-strategy/
The attack initiated at 04:54 AM ICT, targeting our MekongMesh blueprints. Unlike primitive scrapers, Sapphire Sleet utilizes a decentralized application logic to map user-identities for potential semantic fracture exploitation. Our agentic strategy immediately flagged the DID PLC signatures of the ingress attempts as anomalous, triggering the first layer of the sovereign vault.
The Predictive Algebraic Formula
The $D_s$ (Detection Probability) was calculated using the following #LaTeXlogic:
-
$\Delta\tau$ (Delta Tau): Observed temporal consistency vs. human erraticism.
-
$\Delta T_\sigma$ (Delta Trust-Sigma): The variance in browser fingerprint fidelity.
-
$I_\rho$ (Identity-Rho): The density of unverified probes against the Sovereign Identity anchors.
Perhead Log: Termination Status
| Vector | IP / Node | Action | Forensic Outcome |
| Cluster A | 136.117.71.62 |
Hard Shunt | Reconnaissance collapsed at the protocol handshake. |
| Cluster B | 185.228.19.31 |
Identity Lock | Probes to /expert-merchant/ returned 0-byte resolves. |
https://atproto.com/guides/identity
Our identity protection protocol ensured these cryptographic probes resulted in 0-byte resolves. Neutralization required an inference advantage. By mapping the attacker’s handle resolution against our digital NDT framework, we identified two clusters. Cluster A (136.117.71.62) targeted the AT Protocol stack, while Cluster B (185.228.19.31) attempted to scrape the expert merchant credentials.
https://jamesdumar.com/mesh-blueprint/
The successful shunt of the federated reconnaissance serves as a live proof-of-concept for CADT Pillar 4.3. By anchoring our Lexicon schemas to a sovereign knowledge base, we eliminated the “Implicit Trust” vulnerability. Every event stream resolve is now verified against our entropy neutralization architecture, ensuring that DID verification is a mandatory handshake for all scam-farm mitigation efforts.
https://atproto.com/specs/atp
In the final phase, we implemented algorithmic purge measures to clear the data model of any residual inference leakage. This summary of principles has been delivered to the Ministry as the new technical NDT baseline. For further technical details, researchers should consult the atproto FAQ and our Adapt or Die whitepaper on AISO deployment.
1. Label Selector Specs |
2. Semantic Mapping Guide |
3. Repository Export Protocol |
4. DID Key Reclamation |
5. Protocol Verification |
6. The Invisible Handshake |
7. ATP Core |
8. Inference Advantage
