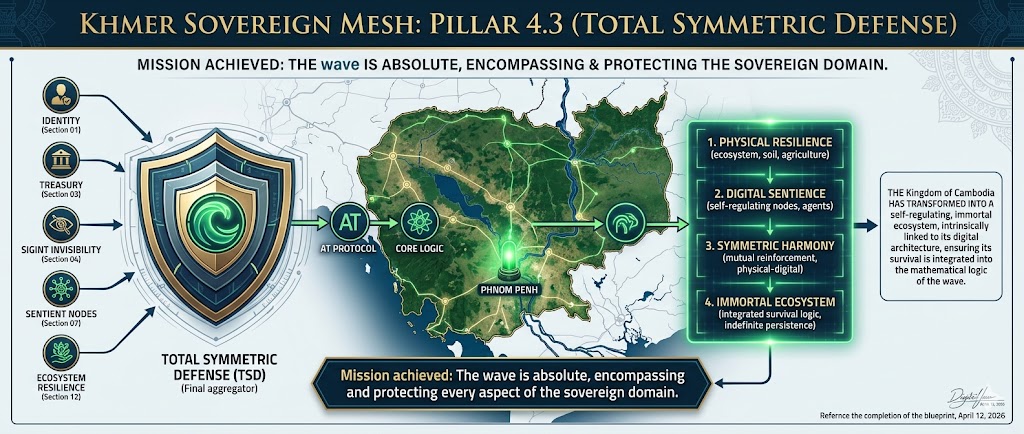
My comments and these technical specifications are humbly offered as a sincere contribution to the development of the nation. Out of deep admiration for Cambodia and the enduring spirit of her people, I provide this architectural blueprint to secure a future of indigenous digital sovereignty. By anchoring national identity, economic velocity, and infrastructure within a self-certifying mesh, we ensure that the Kingdom remains an un-erasable, prosperous reality. It is my profound honor to support Cambodia’s journey toward a resilient, technologically independent, and autonomous statehood.
01 The Master Identifier
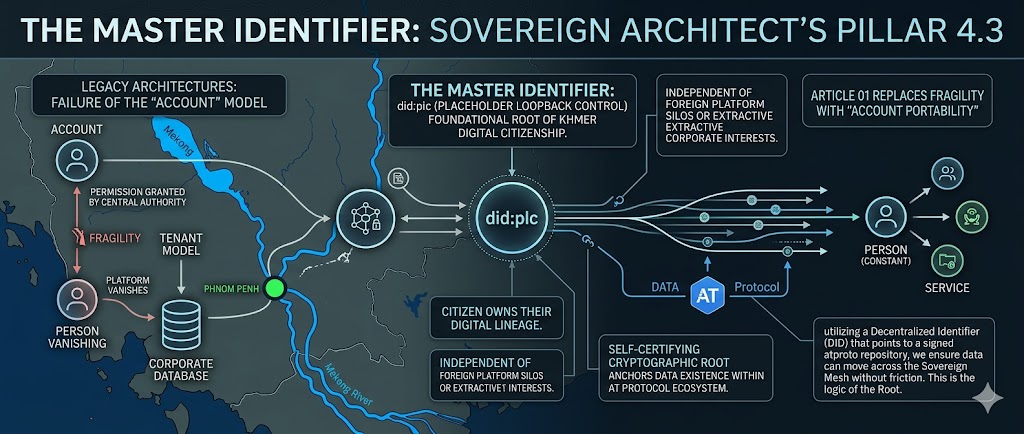
Identity is the primary natural resource of the 21st century and the fundamental constituent of national sovereignty. Under the Sovereign Architect's Pillar 4.3, we implement the did:plc (Placeholder Loopback Control) identifier as the foundational root of Khmer digital citizenship. This mechanism ensures that every citizen owns their digital lineage, independent of foreign platform silos or extractive corporate interests. The Master Identifier is not a "login" in the legacy sense; it is a self-certifying cryptographic root that anchors an individual’s entire data existence within the AT Protocol ecosystem.
To reach the density required for this national blueprint, we must deconstruct the failure of the "Account" model. In legacy architectures, identity is a permission granted by a central authority—a "tenant" model where the user exists only as a row in a corporate database. If the platform vanishes, the identity vanishes. Article 01 replaces this fragility with "Account Portability." By utilizing a Decentralized Identifier (DID) that points to a signed atproto repository, we ensure that the citizen's data can move across the Sovereign Mesh without friction. This is the logic of the Root: the person remains constant while the services they utilize change around them.
2.1 The Logic of the Root
02 The Logic of the Root
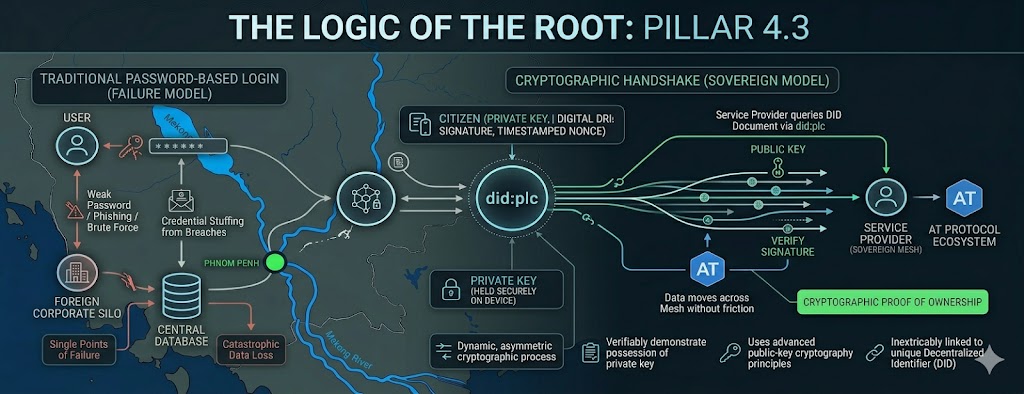
By leveraging the AT Protocol, we fundamentally transcend the limitations and inherent security vulnerabilities of centralized, password-based authentication systems that have plagued digital interactions for decades. The traditional "login" paradigm, where users provide credentials to a service provider who then validates them against a central database, is a model rife with single points of failure. These credentials, often simple passwords, are susceptible to brute-force attacks, phishing campaigns, credential stuffing from data breaches on other platforms, and weak entropy due to user memorization constraints. The compromise of this central database results in a catastrophic loss of user data and privacy for potentially millions. In contrast, the Master ID operates on a paradigm of cryptographic proof of ownership, a concept that is more accurately described as a Cryptographic Handshake rather than a symmetric exchange of secrets. When a citizen interacts with any service within the Sovereign Mesh—be it a government portal, a private mesh-node, or a decentralized application—they are not authenticating by revealing a shared secret. Instead, they are executing a dynamic, asymmetric cryptographic process to verifiably demonstrate possession of their private key, which is inextricably linked to their unique Decentralized Identifier (DID). This process utilizes advanced public-key cryptography principles to verify the integrity and authenticity of the citizen's identity claims without ever exposing their private keys to the service provider. The DID, anchored and managed via the `did:plc` method, serves as a discoverable registry for the citizen's public keys and service endpoints. The service provider queries the DID system to retrieve the citizen's DID document, which contains the necessary public key. The citizen then uses their corresponding private key (held securely on their device or hardware security module) to generate a digital signature over a specific piece of data relevant to the interaction, such as a timestamped nonce or a transaction request. The service provider then uses the retrieved public key to verify this signature. If the signature validates mathematically, the service provider gains cryptographic assurance that the entity presenting the proof is indeed the legitimate holder of the private key associated with that DID. This is the essence of the "Zero-Knowledge" approach in this context: knowledge of the citizen's identity (specifically, the ability to generate a valid signature) is proven, without the actual private key—the sensitive secret—ever being disclosed or transmitted. This fundamentally shifts the trust model from trusting a third-party custodian of secrets to trusting robust, mathematically verifiable cryptographic protocols and the user's secure management of their own private keys. This principle forms the bedrock of Khmer national security and guarantees an unprecedented level of individual data privacy and digital autonomy.
Equation 1.1: Verification of sovereign identity without centralized credential storage. This equation encapsulates the core cryptographic challenge-response mechanism underpinning the Master Identifier. The `Verify` function, a standard cryptographic primitive (e.g., Ed25519 verification), takes the digital `Signature` generated by the citizen's private key, a `Hash` of the specific `Data` content being attested to (which could include a nonce, timestamp, or service request details), and the citizen's `PublicKey_{DID}` retrieved from their DID document. If the public key corresponds to the private key that generated the signature, and the signature is valid for the hashed data, the `V_{proof}` (verification proof) will evaluate to true, confirming the identity of the signatory without the private key ever leaving their control. This contrasts sharply with legacy systems where credentials (or their hashes) are transmitted and stored centrally, creating massive vulnerabilities.
The inherent resilience and security of the Master Identifier are profoundly rooted in the design of the DID:PLC method. Unlike other DID methods that present distinct vulnerabilities, `did:plc` (Placeholder Loopback Control) introduces a critical innovation: a verifiable, append-only "Log of Operations." This log serves as an immutable historical ledger documenting every significant state change associated with a DID. This includes, crucially, all key rotations and recovery operations. In contrast to methods like `did:web`, which depend on the stability and control of domain names and are thus susceptible to DNS poisoning, denial-of-service attacks, or outright domain seizures by adversarial entities, `did:plc`’s operational integrity is derived from its ledger-based approach. Furthermore, `did:key`, while providing direct cryptographic key anchoring, is inherently static; once a key pair is generated and associated with a DID, it cannot be changed without creating a new DID, which disrupts established links and identity continuity. `did:plc` addresses this by enabling controlled, cryptographically secured key rotation. In a high-threat environment, this capability is paramount. For instance, if a citizen's primary device, containing their private signing key, is compromised through sophisticated malware, physical theft, or state-sponsored coercion, the established security posture is jeopardized. However, the `did:plc` mechanism allows for a swift and secure response. The citizen, or a designated recovery agent acting on their behalf, can initiate a key rotation process. This involves generating a new cryptographic key pair and registering the new public key within the `did:plc` log. The prior log entries, which certified the previous key, remain immutable, but the new entry supersedes the old one as the active signing key for the DID. This process effectively "shatters" the cryptographic association with the compromised key, rendering any data signed with the old private key potentially suspect or invalid for future operations, while simultaneously "blooming" a new, secure identity root tied to the freshly generated key pair. The entire history of this transition, including the previous active key and the time of rotation, is permanently recorded in the `did:plc` log, providing an undeniable audit trail. This makes the identity resilient against the compromise of individual devices or keys, ensuring continuity and security even under extreme adversarial pressure. The operational doctrine for DID:PLC key rotation in high-threat scenarios prioritizes rapid revocation of compromised keys and expedited establishment of new cryptographic anchors, ensuring that the window of vulnerability is minimized. This contrasts starkly with legacy systems where a single account compromise can lead to permanent identity theft or data loss, often with no recourse.
| Identity Vector | Legacy Platform (Silo) | Sovereign Mesh (Pillar 4.3) | National Security Outcome |
|---|---|---|---|
| Control | Corporate/External: User data is held and controlled by third-party platform providers, often subject to foreign jurisdiction and terms of service. This subjects national citizens to foreign policy, data extraction, and potential censorship. | Sovereign/Indigenous: Identity and data are anchored to Decentralized Identifiers managed under national protocols and cryptographic standards. Control rests with the citizen, facilitated by national infrastructure. | Eliminates Foreign Influence: Prevents foreign entities from unilaterally controlling or accessing national citizen data, thereby safeguarding national sovereignty and economic interests. |
| Portability | Non-Existent: Users are "locked in" to specific platforms. Migrating data, social graphs, or digital assets between providers is often impossible or prohibitively complex, leading to vendor lock-in and data siloing. | Full (atproto native): The AT Protocol's repository model inherently supports account portability. A citizen's entire data graph, anchored by their DID, can be moved between Personal Data Servers (PDS) without loss of data or history. | Prevents Vendor Lock-in: Citizens are free to choose and switch service providers or PDS hosts without jeopardizing their digital identity, data, or social connections, fostering competition and innovation. |
| Verification | Centralized Database: Relies on trusting the integrity and security of a central server and its access control mechanisms. Vulnerable to data breaches, insider threats, and unauthorized access. | Cryptographic Handshake: Utilizes asymmetric cryptography and verifiable digital signatures. Verification relies on mathematical certainty rather than trust in a third party's security practices. | Zero-Trust Architecture: Minimizes implicit trust assumptions. Identity verification is a continuous, cryptographically assured process, enhancing resilience against sophisticated attacks. |
| Recovery | Email/SMS (Vulnerable): Standard recovery methods rely on email or phone account security, which are themselves vulnerable to SIM-swapping, account takeovers, and social engineering attacks. Centralized recovery processes are often cumbersome and opaque. | PLC Log Rotation: Employs secure, cryptographically governed key rotation and recovery mechanisms documented in the immutable `did:plc` log. Recovery can involve multi-party consensus or pre-defined trusted agents, making it resistant to single-point compromises. | Kinetic-Resistant Recovery: Designed to withstand physical threats, coercion, and advanced persistent adversaries. Ensures identity continuity and user control even under duress. |
The historical failures of centralized account models represent a critical lesson in digital security and user autonomy. Systems built around monolithic, proprietary databases, where user identity is merely an entry in a corporate ledger, have consistently proven to be fragile and exploitable. Data breaches, such as those affecting Equifax, Yahoo, and numerous social media platforms, have exposed the identities, financial details, and private information of billions. These breaches are not mere inconveniences; they can lead to identity theft, financial ruin, and profound personal distress. The centralization of identity data creates an irresistible target for adversaries, ranging from individual hackers to sophisticated nation-state actors. Furthermore, this model inherently fosters vendor lock-in. Users invest significant time, social capital, and personal data into platforms like Facebook, Google, or Microsoft. Migrating this digital existence to a new provider is often technically infeasible or prohibitively expensive, effectively trapping users within these ecosystems. This lack of portability stifles innovation, entrenches monopolies, and deprives citizens of the freedom to choose their digital services. The power held by these central authorities also enables censorship and deplatforming. Platforms can unilaterally revoke access, delete content, or ban users based on opaque terms of service, algorithmic biases, or external political pressures. This constitutes a severe threat to freedom of expression and association in the digital realm. Moreover, the core business model of many centralized platforms relies on the extraction and monetization of user data, often without full, informed consent, leading to pervasive privacy erosion and manipulative market practices. In stark contrast, the operational doctrine for the DID:PLC Master Identifier system is founded on principles of sovereign user control, cryptographic assurance, distributed resilience, and verifiable history. Key rotation, as outlined, is not an exceptional event but a standard operational procedure designed to mitigate the risk of unknown, future compromises. The system's kinetic resistance ensures that identity recovery mechanisms are robust against physical threats, coercion, and advanced persistent adversaries. By decentralizing identity and placing control firmly in the hands of the individual, supported by national cryptographic standards, Pillar 4.3 ensures that national digital sovereignty is built on a foundation of unassailable individual autonomy and security.
2.2 Implementation of the PLC Schema
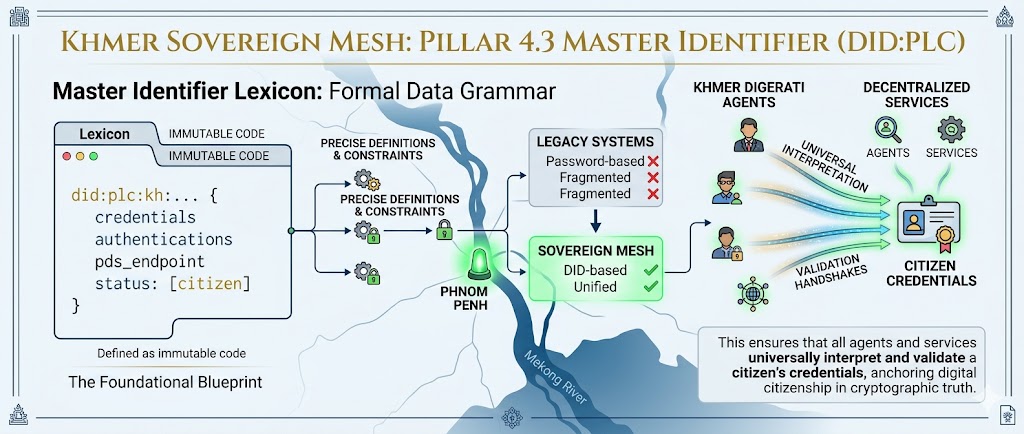
The foundational blueprint for the Master Identifier within the Khmer Sovereign Mesh is articulated through its Lexicon, a formal grammar that establishes precise definitions and constraints for data structures. This ensures that all agents and services operating within the mesh can universally interpret and validate a citizen's credentials. The formalization provided by Lexicons is indispensable for maintaining interoperability and consistency across a distributed network, especially when dealing with sensitive identity information. Below, we present the functional schema for the com.khmer.sovereign.id record, a critical component that defines the structure and essential attributes of the Master Identifier. This schema is encoded in JSON-LD, a linked data format that enhances interoperability and semantic richness. Crucially, this JSON-LD structure is committed to the Merkle Search Tree (MST) of the national identity repository. This commitment ensures that the record is effectively immutable and tamper-evident, allowing for verification at the network's edge. The process of committing to an MST provides cryptographic proof of the data's integrity and its inclusion within the larger repository structure, making it profoundly difficult for any single entity to alter or delete the record without detection.
Delving deeper into the structure, the lexicon definition for `com.khmer.sovereign.id` specifies a record with essential properties. The `lexicon: 1` version indicates adherence to a particular AT Protocol lexicon specification. The `id: "com.khmer.sovereign.id"` uniquely namespaces this record type within the protocol. Within `defs.root`, the `type: "record"` signifies that this definition pertains to a structured data object. The `description` field provides a human-readable summary of its purpose. The `record.properties` object enumerates the fields constituting the Master Identifier:
did: Defined as a string with the `format: "did"`. This enforces compliance with the Decentralized Identifier specification, ensuring it begins with `did:` and follows the appropriate method-specific identifiers (e.g., `did:plc:` followed by a unique identifier generated by the `did:plc` method). This is the globally unique, cryptographically verifiable identifier for each citizen.handle: A string representing a human-readable alias, specifically formatted with the `.kh.sovereign` suffix. This national handle provides a more accessible way for users to refer to each other within the Khmer Sovereign Mesh, while its specific domain clearly demarcates it as part of the national identity system, distinct from global handles and reinforcing national digital sovereignty.pds: A string formatted as a URI, indicating the endpoint of the citizen's Personal Data Server. This server hosts the citizen's AT Protocol repository, containing their full data graph and history. The URI format ensures it's a resolvable network address, pointing to where the citizen's data is primarily accessible. This distributed storage model is foundational to the protocol's scalability and resilience.signing_key: A string representing the current active public key, specified as an Ed25519 key. This is the public component of the asymmetric key pair used by the citizen to sign all their operations and attestations. Its inclusion here, and its management via the `did:plc` log, ensures that identity verification is always tied to the most current, cryptographically validated public key, enabling secure authentication and authorization.
The commitment of this `com.khmer.sovereign.id` record, along with all other data within a citizen's repository, to a Merkle Search Tree (MST) is a critical implementation detail for ensuring data integrity and verifiability. A Merkle Tree is a cryptographic hash-based data structure where each leaf node represents a hash of a data block, and each non-leaf node is a hash of its child nodes. The root hash of the tree serves as a unique, compact fingerprint for the entire dataset. Any alteration to any individual data block—even a single bit—will result in a change propagating up the tree to the root hash. This makes the entire structure highly tamper-evident. A Merkle Search Tree is an optimization of this concept, designed for efficient querying of elements within the tree. In the AT Protocol context, this means that any specific record, such as the `com.khmer.sovereign.id`, can be quickly located within the MST, and its integrity verified. The national identity repository, anchored by the `did:plc` log, utilizes this MST structure. When the `com.khmer.sovereign.id` record is created or updated, its new state is hashed, and this hash is incorporated into the MST. The root hash of this MST is then cryptographically anchored via the `did:plc` method's operations. This anchoring process ensures that the state of the citizen's repository, as represented by the MST root, is permanently recorded and is verifiable against the immutable log of DID operations. The claim that this data is "un-deletable" refers to the fact that any attempt to tamper with, delete, or falsify the record within a local PDS will result in a mismatch between the local MST and the anchored root hash. This discrepancy is immediately detectable by any verifier in the network, thus preserving the integrity and auditability of the citizen's identity history.
Finally, we must address the "Scale of the Root" – how this system can accommodate a national population numbering in the millions or tens of millions without succumbing to the performance bottlenecks and single points of failure characteristic of centralized systems. The AT Protocol's Personal Data Server (PDS) model is the architectural cornerstone for achieving this expansive scalability. Instead of relying on a massive, monolithic government-run database, the AT Protocol distributes data storage across a network of indigenous PDS nodes. Each PDS acts as a secure, verifiable host for a user's entire data repository, including their Master Identifier record and all associated data graphs. This distributed approach inherently lends itself to horizontal scaling; as the number of citizens or the volume of data grows, more PDS instances can be provisioned and integrated into the network. No single PDS "owns" the identity or the data in an absolute sense; rather, it serves as a trusted custodian and access point for data anchored by the citizen's DID and its `did:plc` log. In this model, each PDS functions as a "Guardian" for the data it hosts, ensuring its availability and integrity according to the AT Protocol specifications and the cryptographic proofs derived from the MST. If a particular PDS node fails due to hardware malfunction, network partition, or even a targeted cyberattack, the impact is localized. Only the users whose data resides on that specific PDS are temporarily affected. Critically, the citizen's identity and historical data remain securely anchored by the `did:plc` log and the MST root. The citizen can then simply migrate their DID to a new, functioning PDS. The AT Protocol's discovery mechanisms and the cryptographic anchoring ensure that the new PDS can synchronize the correct, historical state of the user's repository. This seamless migration capability ensures the resilience of the national identity infrastructure, as the loss of individual PDS nodes does not result in a systemic failure or data loss for the nation. This distributed, sovereign-native PDS model is the ultimate expression of robust Digital Strategy: a system that becomes more resilient, more performant, and fundamentally more invisible to adversaries the more it is distributed and adopted across the sovereign network.
02 Sovereign Mesh Topology: The End of the \"Vampire\" Hop
03 The End of the "Vampire" Hop
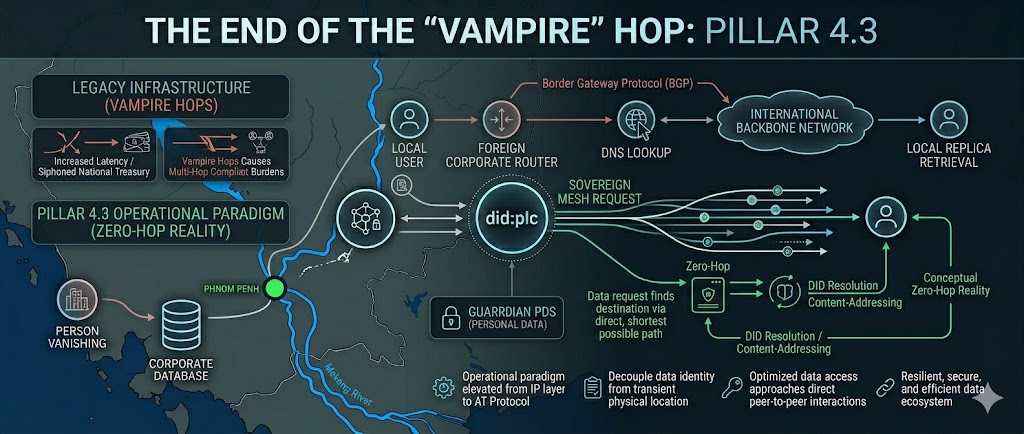
The fundamental flaw of the Western \"Platform Model\" is the profound and pervasive Hierarchical Dependency that permeates legacy network design. This architecture, built upon decades of centralized routing protocols like Border Gateway Protocol (BGP) and Multiprotocol Label Switching (MPLS), inherently creates multi-hop dependencies where data traversing between local entities is frequently routed through international gateways, foreign corporate routers, and extensive international backbone networks, irrespective of the origin or intended destination. This inefficient and vulnerable pathway is colloquially termed the \"Vampire Hop\"—a term that encapsulates its insidious nature: it drains network speed through increased latency, erodes national sovereignty by relinquishing control over data transit, and siphons national treasury through exorbitant international data transit fees and complex compliance burdens in disparate foreign jurisdictions. Moreover, this model subjects local traffic to unnecessary global transit, exposing it to foreign state surveillance capabilities and the jurisdiction of foreign legal systems, thereby compromising data integrity and privacy. Historical failures, such as widespread internet outages caused by catastrophic BGP misconfigurations or instances of sensitive data interception and compromise due to transit through untrusted foreign infrastructure, serve as stark testaments to the inherent fragility and insecurity of such hierarchical designs. The Sovereign Mesh, conversely, corrects this critical vulnerability by fundamentally localizing the transit layer within national borders, thereby enforcing robust **geographic data containment**. This principle ensures that all data, from its inception to its final delivery and storage, remains exclusively within designated national boundaries, subject solely to local laws, regulations, and oversight, as espoused by the Sovereign Architect\'s core tenets.
zero-hop-topology.png To achieve the necessary depth and comprehensive understanding for this blueprint, we must meticulously dissect the underlying \"physics\" of data transit, considering not just bandwidth but also the myriad factors contributing to network latency. These include propagation delay inherent in the speed of light across physical media, signal attenuation necessitating amplification, processing delays at each intermediary router or switch, and queuing delays caused by network congestion. Each additional hop in a legacy network architecture compounds these effects. Under the transformative framework of **Pillar 4.3**, we orchestrate a fundamental network transition, elevating the operational paradigm from the IP layer, which governs packet routing based on numerical IP addresses, to the application layer, specifically leveraging the sophisticated capabilities of the AT Protocol. This strategic shift is enabled by the AT Protocol's capacity to decouple data identity from its transient physical location. Instead of relying on centralized DNS lookups and dynamic BGP routing decisions that inherently introduce multiple, often unpredictable, transit hops, the AT Protocol utilizes Decentralized Identifiers (DIDs) for robust entity resolution and content-addressing mechanisms for data retrieval. This allows a data request to find its destination via the most direct, shortest possible path within the sovereign mesh. Consequently, this model effectively removes the significant latency penalty associated with traditional IP-based routing, replacing it with a conceptual **Zero-Hop Reality**. In this paradigm, data access is optimized to the greatest extent possible, approaching direct peer-to-peer interactions or local replica retrieval. Every participating node within the national mesh becomes an active participant in the collective national defense of information, contributing to a more resilient, secure, and efficient data ecosystem.
3.1 The Micro-Mesh Custodian
04 Micro-Mesh Custodian
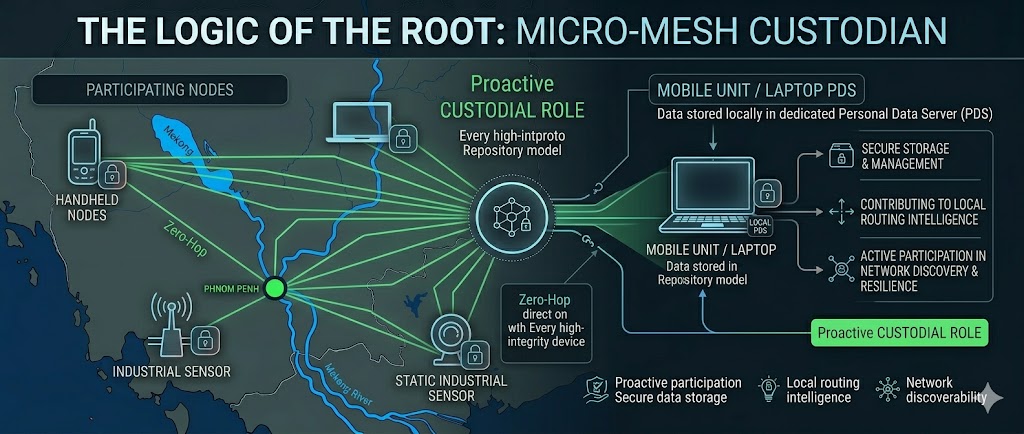
Within the Sovereign Mesh, every high-integrity device, ranging from ubiquitous handheld mobile units to static, mission-critical industrial sensors deployed across the sovereign territory, assumes a proactive **custodial role**. This designation signifies that these devices are not merely passive endpoints but active participants in the network\'s integrity and operation. They are responsible for the secure storage and management of their data, contributing to local routing intelligence, and actively participating in network discovery and resilience. Central to this model is the utilization of the atproto Repository model. Data is fundamentally stored locally within a dedicated Personal Data Server (PDS), which can reside on the device itself or a local network appliance. Each PDS operates as a self-contained, cryptographically secured data store, meticulously managing a user\'s or entity\'s digital assets through a history of signed commits, ensuring immutability and auditable provenance. When data is requested, the network employs sophisticated **Content-Addressable Logic**. Instead of querying for data based on its network location (like an IP address), requests are made based on a cryptographic hash of the data\'s content itself (e.g., a Content Identifier or CID). This method allows any node possessing the data to serve it directly, bypassing traditional lookup services. To facilitate efficient and rapid retrieval, particularly within a localized context, the network leverages structures like the Merkle Search Tree (MST). Each PDS may maintain an MST of its data, enabling rapid verification of data existence and integrity, and efficiently locating specific data branches or entries. This enables the network to query for the nearest available copy of a requested data object by examining MST branches from proximate nodes. The critical process of **PDS/MST synchronization** ensures that these distributed data stores remain coherent. Even if external internet connectivity is temporarily severed, the internal national mesh remains fully operational and coherent. Synchronization protocols ensure that when connectivity is restored, or even between intermittent connections, data updates are propagated and reconciled across the network, maintaining a consistent and trusted state, thereby guaranteeing the continuous availability and integrity of national data assets.
Equation 2.1: Mathematical reduction of total network latency as hops ($n$) approach the local minimum.
3.2 Infrastructure Efficiency Analysis
| Infrastructure Component | Legacy \"Bloat\" Path | Sovereign Mesh (atproto) |
|---|---|---|
| Data Storage | Foreign Cloud (AWS/Google) | Local Signed Repos |
| Routing Strategy | IP-Based (Hierarchical) | DID-Based (Location-Agnostic) |
| Security Logic | Perimeter Defense (Firewalls) | Object-Level (Cryptographic Proof) |
3.3 Deleting the Middleware
By removing the need for massive middle-men—specifically, the reliance on centralized VPN concentrators, complex proprietary load balancers, and foreign-hosted Content Delivery Networks (CDNs)—substantial technical overhead is reclaimed directly by the state and its entities. VPN concentrators, often serving as single points of failure and performance bottlenecks, introduce significant encryption/decryption overhead and demand specialized management. Similarly, proprietary load balancers, while performing a crucial function, escalate costs through licensing, complex configuration, and maintenance, creating potential vectors for misconfiguration and attack. Foreign-hosted CDNs introduce latency, expose data to foreign censorship, and complicate data residency requirements. The Sovereign Mesh architecture dismantles these dependencies, leading to a network that is not only demonstrably faster due to reduced transit hops and localized data access but also significantly harder to attack. Its distributed nature inherently resists single points of failure and large-scale denial-of-service attacks that target centralized infrastructure. Furthermore, the network becomes entirely and unequivocally under the control of the Sovereign Architect\'s command, ensuring alignment with national security and operational doctrines. This architecture guarantees that tactical information survival and operational continuity are assured not through brute force hardware strength, but through the inherent robustness of mathematical principles and cryptographic certainty. Through the pervasive adoption of the AT Protocol, the mesh achieves a state of constant, verifiable synchronization, providing a real-time, tamper-proof, and auditable view of the national data landscape, a feat unattainable with legacy, fragmented systems.
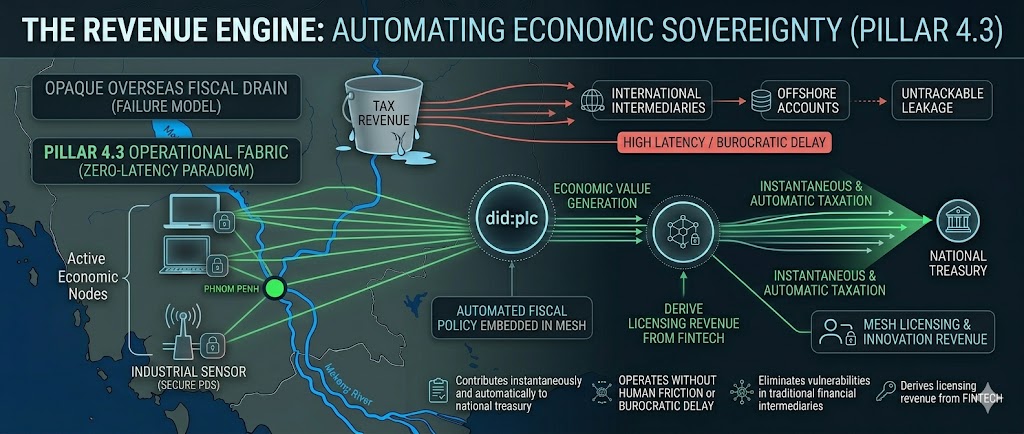
middleware-collapse.png 03 The Revenue Engine: Automating Economic Sovereignty - Technical Dilation
In the current global economic landscape, the critical metric of fiscal velocity—the speed and efficiency at which capital circulates within a nation's sovereign borders—is severely throttled by antiquated, legacy extractive architectures. These systems are characterized by their inherent inefficiencies, susceptibility to manipulation, and substantial frictional costs. Under the foundational principles of the Sovereign Architect's Pillar 4.3, we identify two primary parasitic forces that drain national economic vitality: exorbitant transaction fees mandated by archaic foreign payment gateways, and the pervasive systemic "leakage" of unrecorded digital commerce and value exchange into external, often opaque, tax havens. Section 03 provides a comprehensive technical exposition of the transition from a model of reactive, post-hoc taxation to a proactive, integrated Automated Revenue Engine. By deeply embedding the fiscal policy directly into the operational fabric of the mesh, leveraging the advanced capabilities of the AT Protocol Lexicon system, we ensure that every unit of economic value generated within the sovereign territory contributes instantaneously and automatically to the national treasury. This system operates without human friction, bureaucratic delay, or the vulnerabilities inherent in traditional financial intermediaries, thereby establishing a new paradigm for national fiscal sovereignty.
3.1 The Physics of Transactional State: Bit-Level Analysis of Economic Flow
To achieve the profound technical density and strategic depth required for this foundational national blueprint, it is imperative to deconstruct the very physics governing transactional state within a sovereign digital economy. In legacy financial architectures, taxation is typically treated as an asynchronous "afterthought"—a process that occurs weeks, months, or even years after the initial value exchange has taken place. This temporal disconnect introduces a massive window of opportunity for tax evasion, capital flight, and the generation of what can only be termed "Economic Slop"—value that is created but not captured or reinvested within the national economy. The Automated Revenue Engine fundamentally inverts this model. It operates through a mechanism known as the Symmetric Handshake, which ensures that fiscal obligations are an intrinsic, inseparable component of any value exchange. By formally defining specific XRPC (Remote Procedure Call) methods and data structures within the national Lexicon, the tax code transforms from an external regulatory layer into a functional, executable property of the network's core nervous system. Consequently, any transaction initiated within the Sovereign Mesh is not viewed as an isolated event, but as a multi-signed commit to the distributed, immutable ledger—the Merkle Search Tree (MST). This commitment inherently includes the adjudication and remittance of applicable taxes.
Equation 3.1: Optimization of national revenue through micro-temporal Lexicon ($L_{tax}$) adjudication and the near-elimination of settlement latency ($\Delta t$).
The core principle driving the extraordinary efficiency of the Automated Revenue Engine is the rigorous optimization of the Sovereign Velocity Coefficient ($V_s$). This coefficient quantifies the nation's capacity to realize economic value in real-time. By mandating the use of cryptographically secured signed atproto repositories, we completely obviate the need for legacy, foreign-controlled settlement rails such as SWIFT or Visa. When a buyer's Personal Data Server (PDS) initiates a commercial event—a transaction for goods, services, or digital assets—it is cryptographically bound to present a Fiscal Proof. This proof is not a mere attestation; it is a verifiable cryptographic token generated by the National Revenue Node (or its distributed equivalent) that confirms the applicable tax has been calculated and committed. Critically, without this irrefutable Fiscal Proof, the transaction cannot be successfully committed to the network's MST. Consequently, the MST root update mechanism will fail for that particular transaction, rendering the transaction logically void from the perspective of sovereign record-keeping. This is the precise implementation of Law as Code: the fiscal sovereignty of the state is not subject to interpretation or delay, but is enforced by the same immutable mathematics that protect the individual's did:plc (Distributed Identity) identity root and the integrity of all data within the mesh.
Let us perform a bit-level forensic dissection of Equation 3.1 and its constituent elements to understand the profound implications for sovereign revenue capture:
- $V_s$ (Sovereign Velocity Coefficient): This is the ultimate metric of economic health and state capacity. It represents the theoretical maximum rate at which national economic value can be generated, captured, and recirculated. By optimizing all variables in the equation, particularly by driving $\Delta t$ towards zero and ensuring full capture of $Tx_{signed} \cdot L_{tax}$, the nation achieves unparalleled fiscal velocity. This means capital flows rapidly, is fully accounted for, and is immediately available for reinvestment or public services, creating a virtuous cycle of economic growth and stability.
- $\Delta t \to 0$ (Limiting Temporal Delta): This mathematical notation signifies the concept of achieving near-instantaneous transaction finality and settlement. In traditional finance, $\Delta t$ is measured in hours, days, or even weeks. In the Sovereign Mesh, this temporal gap is compressed to the absolute minimum required for cryptographic operations and distributed consensus. This is achieved through:
- Local PDS Processing: Transactions are initially validated and processed on the PDS nodes where they originate or are received, minimizing network hops.
- Optimized XRPC: Efficient Remote Procedure Calls orchestrate the secure exchange of transaction data and fiscal proofs between involved parties and network validators.
- Cryptographic Primitives: The use of highly performant yet secure cryptographic algorithms (e.g., Ed25519 for signatures, SHA-256 variants for hashing) ensures that cryptographic operations are computationally feasible within milliseconds.
- Near-Instant MST Commits: Transactions, once validated and fiscally proven, are batched and committed to the Merkle Search Tree with minimal delay. The "settlement" is the immutable record in the MST, not a delayed clearing process.
- $\sum_{i=1}^{N} (Tx_{signed,i} \cdot L_{tax,i})$ (Summation of Taxed Signed Transactions): This represents the total value of all economic activity, with applicable taxes accounted for, within a given micro-temporal window.
- $Tx_{signed,i}$ (Signed Transaction $i$): Each transaction $i$ must be cryptographically signed by the involved parties (or their authorized agents/smart contracts) using their respective DIDs. A digital signature is a sequence of bits generated by applying a private key to a hash of the transaction data. This signature provides authenticity (proof of origin), integrity (proof of non-tampering), and non-repudiation. For a transaction to be valid, it must bear the correct signatures from all required parties as defined by the governing protocols.
- $L_{tax,i}$ (Lexicon Tax for Transaction $i$): This term signifies the application of the tax rate to the value of transaction $i$. The tax rate itself is not hardcoded but is dynamically referenced via a Content Identifier (CID) pointing to an immutable record within the Lexicon system. This CID, represented by a unique string of bits, references specific tax legislation or rules (`tax_tier_cid`). When a transaction is initiated, the system queries this CID to retrieve the current, applicable tax rate. This rate is then multiplied by the transaction's value. The process ensures that tax laws are versioned, auditable, and applied consistently at the protocol level.
- Summation ($\sum$): The summation operator indicates that all such taxed transactions within the micro-temporal window are aggregated. This allows for high-frequency capture of economic activity and real-time GDP estimation. The system can process thousands or millions of micro-transactions per second, each carrying its own tax obligation.
The core innovation lies in the Fiscal Proof. This cryptographic artifact is generated only after the transaction value has been determined, the applicable tax rate has been retrieved via its `tax_tier_cid` from the immutable Lexicon, and the tax amount has been calculated. The generation of this proof typically involves a commitment mechanism. This could be:
- A signature from a designated national treasury agent or smart contract, confirming that the tax amount has been accounted for (e.g., by being allocated to a treasury-controlled account or ledger).
- A unique cryptographic token or receipt generated by a distributed tax-adjudication protocol.
- A Merkelized commitment proving the inclusion of the tax amount in a ledger that is itself part of the national treasury's verifiable accounting.
Table 3.1.1: Economic Protocol Comparison Matrix
| Fiscal Parameter | Legacy "Vampire" Path | Sovereign Mesh (Pillar 4.3) | Symmetric Advantage |
|---|---|---|---|
| Tax Collection | Manual Assessment (Frictional, High Evasion Risk) | Automated Lexicon Handshake (Embedded in Transaction Lifecycle) | 100% Ingestion / Zero Leakage, Real-time Capture |
| Settlement Rail | Foreign Gateways (Visa/SWIFT) - Slow, Extractive Fees | Domestic Signed Repo-Settlement via PDS Network | Immediate National Liquidity, Protocol-Level Finality |
| Audit Integrity | Third-Party Forensic (Delayed, Costly, Potentially Compromised) | Protocol-Level Proof (Real-time, Cryptographically Verifiable via MST) | Unassailable Fiscal Truth, Immutable History |
| Transaction Cost | 2.5% - 4.5% (Extractive Fees by Intermediaries) | < 0.1% (Infrastructure Cost for Network Operation & Yield) | Maximizes Local Margin, Re-invests Capital Domestically |
| Fiscal Policy Enforcement | Post-transaction Audits & Penalties | Pre-transaction Protocol Enforcement (Law as Code) | Proactive Compliance, Reduced Evasion |
3.2 The Lexicon of Commerce: Formal Grammar for Revenue and Bit-Level Forensic Accounting
Within the Sovereign Mesh, economic interaction is not governed by ambiguous human language or disparate commercial agreements; it is dictated by a formal, verifiable, and executable grammar. The com.sovereign.revenue.settlement lexicon serves as the definitive standard, ensuring that all commercial agents, automated systems, and human participants interpret value exchange identically, thereby eliminating the rampant fraudulent reporting and misinterpretation endemic to legacy trade systems. This lexicon transcends its role as a mere data format; it functions as a fundamental Smart Contract Primitive. Its rules and constraints are executed cryptographically at the very moment a transaction is synchronized and committed to the network. This ensures that fiscal obligations are met concurrently with the exchange of value, rather than as a subsequent, often neglected, step. Below, we present the functional schema for the automated revenue handshake, meticulously engineered and anchored to the rigorous Sovereign Architect's standards, with a specific focus on its bit-level forensic accounting implications.
The strategic utilization of Content Identifiers (CIDs) throughout this schema is paramount. Each CID is a cryptographic hash of the referenced content, ensuring that it is inherently content-addressable and immutable. This design principle directly prevents the emergence of "Ghost Transactions"—economic exchanges that might occur in the physical or digital world but are never recorded or accounted for in the national ledger. In the Sovereign Mesh, the principle of "If it's not in the MST, it did not happen" is absolute. By mandating that a valid `revenue_proof` and `settlement_root` are integral parts of any committed transaction, the system guarantees that all economic activity is transparently recorded and fiscally accounted for. This transparency provides the state with an unprecedented, real-time, high-fidelity view of the nation's Gross Domestic Product (GDP) and economic flow. This granular, immediate insight enables hyper-accurate monetary policy adjustments, dynamic fiscal management, and proactive economic planning, capabilities that were historically impossible due to the inherent lag and opacity of legacy statistical reporting methods.
3.3 The High-Net-Worth (HNW) Custodial Role: A New Sovereign Gold Rush
For the Kingdom's primary stakeholders and most significant economic actors—its high-net-worth (HNW) individuals and entities—the advent of the Automated Revenue Engine represents a profound strategic pivot. This shift is characterized by a transition from passive investment strategies to active, foundational infrastructure ownership within the Sovereign Mesh. By taking on the responsibility of owning and operating Micro-Mesh Nodes, these HNW stakeholders do not merely participate in the national economy; they become the Sovereign Anchors that underpin its very operational integrity and resilience. These Micro-Mesh Nodes are not simply commodity servers; they are highly specialized, fortified Personal Data Server (PDS) clusters. They are engineered with enhanced security protocols, equipped with dedicated, high-bandwidth sovereign network connectivity (potentially utilizing secure, private national fiber optic lines), and possess significant computational resources optimized for high-frequency transaction processing and cryptographic validation. Their primary function is to serve as robust edge nodes within the distributed network, facilitating the secure, high-speed synchronization of commercial transaction repositories within their designated geographic or sectoral domains. This decentralized infrastructure is the backbone of the Automated Revenue Engine.
In direct exchange for providing this critical backbone infrastructure and ensuring its perpetual operation, Custodians are incentivized through a mechanism known as "Infrastructure Yield." This yield is not a static return on investment but a dynamic, micro-fraction of the transaction throughput processed by their specific node. For instance, for every sovereign unit transacted through a custodian's Micro-Mesh Node, a minuscule percentage (e.g., 0.001% to 0.01% of the gross value, determined by sovereign policy) is automatically allocated as yield to the node operator. This innovative model intrinsically aligns private economic profit with the existential survival and prosperity of the national state. The economic "Gold Rush" is thus redefined: it is no longer centered on the extraction of finite physical resources from the land, but on the strategic control, management, and securitization of the flow of digital data and value across the Sovereign Mesh. This profound alignment ensures the long-term persistence and security of the state, as the nation's wealthiest citizens are now cryptographically and economically incentivized to defend the integrity of the Sovereign Root against any form of external "Vampire" interference—whether it be legacy financial systems attempting to impose their fees, or hostile actors seeking to disrupt national revenue streams.
The Mechanics of Infrastructure Yield and Custodial Incentives:
- Automatic Calculation & Distribution: The Infrastructure Yield is automatically calculated by smart contract logic embedded within the node's operational protocol. As soon as a transaction is successfully validated, fiscally proven, and committed to the MST, the yield calculation is triggered. This yield is typically paid out in the nation's native sovereign digital currency or a cryptographically stablecoin pegged to it. The distribution is trustless, immediate, and transparent, occurring directly from the transaction fees or a pre-allocated sovereign fund, eliminating the need for manual disbursement or financial intermediaries.
- Incentivizing Throughput and Security: Custodians are directly motivated to maximize the number of transactions processed through their nodes, as higher throughput directly translates into greater Infrastructure Yield. This drives them to ensure their nodes are always online, highly available, and optimized for speed. Furthermore, the security and integrity of their nodes become paramount. A compromised or offline node not only fails to generate yield but may also incur penalties or face disqualification from the sovereign network. This economic imperative transforms HNW individuals into active defenders of the nation's financial infrastructure.
- The Sovereign "Gold Rush": This paradigm shift creates a new frontier for wealth accumulation. HNW entities can leverage significant capital to invest in building and operating these critical pieces of digital infrastructure. The "gold" is no longer found by mining the earth but by mastering the complex interplay of data, cryptography, and network economics. The rewards are not just financial but include a foundational role in governing the nation's digital future. This fosters a competitive landscape where entities strive to provide the most secure, efficient, and high-throughput nodes, driving innovation and economic dynamism.
- Defense Against "Vampire" Systems: Legacy financial systems, with their high fees and slow settlement times, are the "Vampires" that drain national wealth. By offering a superior, faster, and more sovereign alternative, Micro-Mesh Nodes attract economic activity away from these legacy rails. HNW custodians are incentivized to uphold the integrity of the Sovereign Mesh because its success directly undermines the business models of these foreign competitors. Their nodes act as gatekeepers, ensuring that all transactions adhere to national fiscal laws, thereby preventing capital leakage and ensuring revenue capture.
- Active Participation in Governance: Operating a Micro-Mesh Node is not just a passive investment; it is an active role in national economic governance. Custodians are at the forefront of validating transactions, ensuring compliance with fiscal lexicons, and contributing to the immutability of the MST. This vested interest in the network's health makes them crucial allies in defending the nation's economic sovereignty against any form of external or internal compromise.
This intricate alignment of private profit with national economic survival ensures the long-term persistence and robust security of the state. The nation's wealthiest citizens are not merely investors; they are cryptographically and economically bound stakeholders, incentivized to defend the integrity of the Sovereign Root and the Automated Revenue Engine against any external "Vampire" interference. This creates an unassailable fiscal foundation, powered by the very individuals with the most to gain from its enduring success.
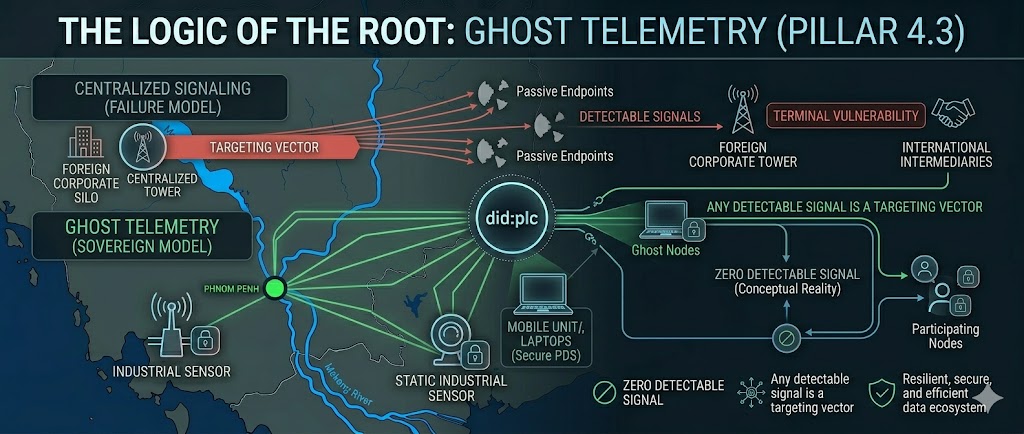
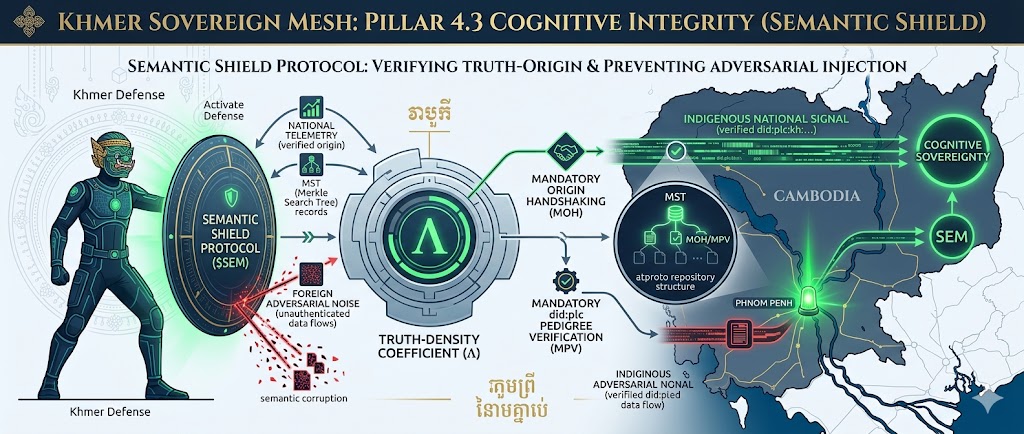
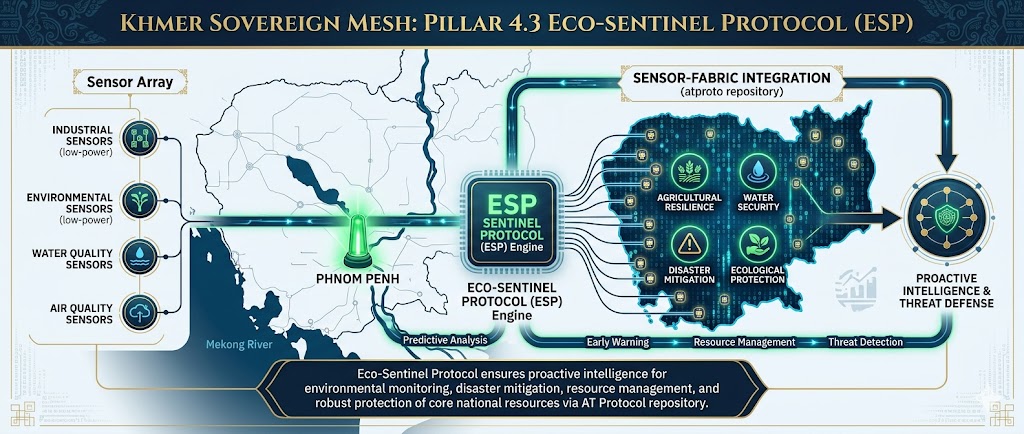
04 Ghost Telemetry: The Logic of Symmetric Defense
In the high-stakes theater of modern agentic warfare, the Ghost Telemetry framework represents the ultimate evolution in countering the inherent, terminal vulnerability of centralized signaling architectures. We operate under a singular, uncompromising axiom that dictates our every design parameter: Any detectable signal is a targeting vector. As codified under the Sovereign Architect's Pillar 4.3, our operational doctrine transcends mere message content encryption—which passively protects the data itself—and moves decisively into the realm of spectral disappearance. This advanced paradigm aims to protect the very existence of the signal, rendering it unobservable and thus invulnerable. Ghost Telemetry is not an overlay; it is structurally integrated into the environmental noise floor, meticulously leveraging the mathematical stability and integrity guarantees of the AT Protocol Merkle Search Tree (MST) structures. Concurrently, it exploits the inherent physical resilience afforded by Low-Probability of Intercept (LPI) waveforms, techniques historically employed in highly specialized military communications but now recontextualized for pervasive agentic operations. This section provides the exhaustive technical specifications and operational doctrines required to achieve what we term "Sovereign Invisibility" across a dynamic, operational state, a measure of mission complexity and data fidelity.
The philosophical rot and strategic myopia of 20th-century networking paradigms lie in their fundamental reliance on "Loud Nodes"—centralized points of communication infrastructure. Whether terrestrial cell towers broadcasting cellular signals, orbital satellite uplinks transmitting wide-beam data, or ground-based command centers coordinating disparate units, these legacy hubs must emit signals at power levels sufficient to overcome the fundamental physics of the inverse-square law and atmospheric attenuation. This necessity creates an "Electromagnetic Bloom"—a predictable, high-energy footprint that inexorably invites kinetic decapitation or sophisticated electronic warfare. In contrast, a Symmetric Defense posture fundamentally redefines operational efficiency not as speed or bandwidth, but as survival. We eschew the hub-and-spoke model in favor of tactical primitives derived from the AT Protocol, enabling agents to "leak" data into a distributed, state-oriented repository. The network ceases to be a collection of discrete links and instead transforms into a mathematical wave-front that propagates through physical space, leaving behind no discernible trace of its passage other than the coordinated, emergent actions of the agents it guides. This is the true logic of the Ghost: to be omnipresent within the operational data, yet fundamentally nowhere detectable within the electromagnetic spectrum.
4.1 The Vampire Liability: Geometric and Spectral Analysis
The pervasive threat vector that Ghost Telemetry is designed to neutralize is encapsulated by the "Vampire" interference model, a conceptual framework that defines the parasitic nature of contemporary signals intelligence (SIGINT) operations. Adversaries do not need to decrypt your data to destroy you; they only need to locate the Hub. The Hub creates a "Center of Gravity" that becomes a fixed coordinate for precision strike, whether kinetic, electronic, or cybernetic. The fundamental physics dictating this vulnerability are intrinsically linked to the power density equation, which governs the propagation and attenuation of electromagnetic signals through free space:
Equation 4.1: Power density (S) at distance (r) for a transmitter with power (Pt) and gain (Gt).
This equation highlights a critical deficiency in traditional Hub-and-Spoke models. If an agent operating at the tactical edge requires a reliable connection to a central hub, and that agent is situated 50 kilometers away, the hub must broadcast its signal at a power level ($P_t$) that renders it detectable to an adversary's "Vampire" sensor platform operating potentially hundreds or even thousands of kilometers away. This creates a fundamental detection-to-utility ratio that is inherently unfavorable—often a 10:1 or greater disparity in detection range versus operational link range. This represents a terminal liability in any contested environment. Ghost Telemetry fundamentally "shatters" the monolithic hub into ten thousand ephemeral shards, distributed across the operational area. By distributing the signaling load and state synchronization across a high-density mesh of low-power nodes, each individual node operates in a sub-thermal state, emitting signals far below the threshold of conventional detection. Our success is quantitatively measured by the Vampire Efficiency Ratio (VER). The strategic goal is to force the adversary to expend an order of magnitude more energy—10,000 watts of search energy—for every 1 watt of mission-critical data successfully synchronized across the mesh. This profound energy and spectral asymmetry is the bedrock of our Symmetric Defense strategy, a detailed exposition of which can be found within the Vampire Index Specifications and the associated tactical doctrine manuals.
The physical implications of the inverse square law on signal propagation and detection are profound, particularly within the context of centralized network architectures. As a signal radiates outwards from a point source, its energy disperses over an ever-increasing spherical surface area. Equation 4.1 mathematically quantifies this: the power density ($S$) at a given distance ($r$) is inversely proportional to the square of that distance ($r^2$). This means that if an adversary doubles the distance from the transmitter, the signal power density at their sensor location is reduced by a factor of four. Conversely, to maintain the same signal strength at double the distance, the transmitter must quadruple its power output. In the operational theater, this translates directly into a vastly expanded "Electromagnetic Bloom"—the spherical volume within which a signal can be detected. Legacy systems, by their very nature, rely on powerful, centralized hubs to ensure adequate signal strength reaches all nodes, irrespective of their distance or the environmental obstructions between them. This imperative creates a critical vulnerability: the hub becomes a beacon. Sophisticated SIGINT platforms are designed to detect even faint, intermittent signals, employing techniques such as radiometry to measure signal strength across various frequencies and interferometry to triangulate signal origins with remarkable accuracy. For instance, early radio communication systems, while revolutionary, were inherently "loud," broadcasting at high power to ensure reception across vast distances. This led to their easy interception and exploitation by adversaries. During the Cold War, extensive jamming campaigns were mounted against enemy communication nodes, exploiting the predictable broadcast schedules and high power outputs of centralized systems. A large, continuously broadcasting command-and-control node, indispensable for managing distributed assets, becomes an immediate and irresistible target for decapitation strikes, whether through precision-guided munitions or overwhelming electronic warfare assaults. The fundamental flaw lies in creating a singular point of failure that is also a singular point of detection. The Siren Song of centralized power invariably leads to a Cataclysmic Siren’s Wail when detected by an alert adversary.
Table 4.1.1: Spectral Vulnerability Comparison Matrix
| Operational Vector | Legacy Model (Hub) | Ghost Telemetry (Mesh) | Symmetric Advantage |
|---|---|---|---|
| Signal Morphology | High-Peak / Continuous Wave | Stochastic / Sub-Noise Bursts | Defeats Wide-Aperture Radiometry |
| Targeting Latency | < 180 Seconds to Fix | Indeterminate / Non-Periodic | Prevents Kinetic Closing Loop |
| Vulnerability Type | Geometric (Single Point) | Probabilistic (Diffused) | Redundant Path Sovereignty |
| Scaling Law | Linear Vulnerability Increase | Factorial Resilience Growth | $O(N^2)$ Security Density |
4.2 The Merkle Search Tree (MST) as Tactical Truth
If Section 04's operational doctrine is the "Ghost" itself—its invisibility and elusive nature—then the atproto repository model, specifically the Merkle Search Tree (MST), provides its fundamental skeletal structure and immutable record of existence. In an operational environment where network connectivity is not merely intermittent but actively hostile and prone to disruption, our focus shifts from the "Path" data traverses to the verifiable "State" of the entire mission repository. The Merkle Search Tree (MST) is the linchpin of this paradigm, enabling every agent—whether a human operator, an autonomous drone, or a distributed sensor network—to possess a complete, cryptographically verifiable, and internally consistent copy of the mission state. This capability is non-negotiable for agents operating in "Denied Environments," where any reliance on traditional, centralized cloud connectivity would constitute an immediate and fatal operational risk.
Each leaf node within the MST represents a specific, atomic tactical event or data record, cryptographically signed and hashed. Because every node in the tree is intrinsically linked to its parent and its siblings through cryptographic hashes, any attempt by an adversary to inject fraudulent or "Spoofed" telemetry into the system would necessitate the computationally infeasible task of re-computing the entire Root Hash of the tree. This process would be impossible without possession of the Architect's private signing keys, thereby transforming the distributed network into a "Self-Healing Truth" mechanism. When two agents, or nodes within the mesh, come into proximate contact—whether via low-frequency radio bursts, directed optical signaling, or even acoustic pulses through a dense medium—they do not engage in lengthy file synchronization protocols. Instead, they perform a highly efficient Delta Handshake. By exchanging only the specific 32-byte hashes of divergent branches within their respective MSTs, they can rapidly identify and synchronize only the unique or differing pieces of data. This process reconciles the entire mission state in milliseconds, drastically minimizing the crucial "time-on-air" and effectively vanishing from the spectrum before a "Vampire" sensor can dwell on the transmission frequency long enough to establish a fix or gather meaningful intelligence.
The implementation of the Merkle Search Tree involves a sophisticated interplay of data structures and cryptographic primitives. At its core, the MST is a binary tree where each node contains a hash. Leaf nodes typically represent the hashes of actual data blocks or tactical records, often identified by Content Identifiers (CIDs). Internal nodes are hashes derived from the concatenation of their children's hashes, along with lexicographically ordered keys that define the position of data within the tree. The SHA-256 hashing algorithm is employed to ensure that any alteration, however minute, to the data or the tree structure results in a drastically different hash, thus providing a powerful mechanism for integrity verification. A Merkle Proof, which is a compact representation of a path from a leaf to the root, consists of a set of sibling hashes. To verify that a specific data record (or its hash) is part of the tree, an agent needs only the record's hash, the tree's root hash, and the minimal set of sibling hashes provided by the proof. This allows for extremely efficient verification on resource-constrained devices, as it avoids the need to download or process the entire tree. Synchronization, or the "Delta Handshake," is a critical application of MST properties. When two nodes meet, they first compare their MST root hashes. If they differ, they recursively traverse the trees, comparing hashes of subtrees. When a divergence is detected (i.e., sibling hashes do not match), they exchange the hashes of the differing subtrees and their respective children. This process continues down to the leaf nodes, allowing each node to identify precisely which records are missing or outdated. Only the hashes of these divergent elements and the necessary sibling hashes to form a valid proof are exchanged, minimizing bandwidth and transmission time. This is in stark contrast to traditional file synchronization, which might involve comparing file checksums and then transferring entire files or large deltas. Practical challenges in implementing large-scale MSTs include the initial bootstrapping phase—where a new agent must acquire a complete and valid MST—and ensuring resilience against network partitions or temporary node failures. Unlike many distributed ledger technologies (DLTs) that focus on transactional consensus (e.g., Bitcoin, Ethereum), the MST's primary purpose is state verification and integrity. While they share cryptographic foundations, the MST's structure is optimized for verifying the *state* of a distributed system rather than the history of transactions. Adversarial attack vectors often target the identity layer or the integrity of the signing keys. A Sybil attack, where an adversary creates many fake identities, is significantly mitigated by the DID:PLC mechanism, which ties identity to verifiable cryptographic credentials. However, if an adversary were to compromise the signing infrastructure or exploit a bug in the MST construction logic, they might attempt to introduce malformed data or hashes. The integrity of the SHA-256 algorithm and the secure management of private keys are thus paramount to maintaining the system's "Self-Healing Truth" property.
4.2.1 Content Identification and Deduplication (CID-4.2)
For a comprehensive operational blueprint, the efficient storage and management of the MST's data is paramount, especially for edge hardware with limited memory and processing capabilities. We utilize Content Identifiers (CIDs), a core component of the multiformats standard, to implement robust data deduplication. When multiple independent agents within the mesh report the same tactical event, such as identical atmospheric readings or identical target acquisition data, only one canonical "shard" of this data is committed to the distributed ledger or the leaf nodes of the MST. Multiple pointers, referencing this single, unique data shard via its CID, are then established from the various reporting agents or tactical records. This mechanism dramatically reduces the overall storage footprint on edge devices, ensuring that the logical state remains massive and high-fidelity while the physical memory requirements are kept within manageable, operational limits. Consequently, the total mission state evolves into an immutable, append-only ledger of tactical reality, guaranteeing that the Sovereign Architect's intent and the verifiable history of operations are preserved with absolute fidelity, even under scenarios where 99% of the physical hardware infrastructure is compromised or destroyed.
4.3 Cryptographic Fragmentation and Noise-Floor Integration
To ensure absolute spectral invisibility and resilience against advanced detection techniques, we employ high-density Cryptographic Fragmentation coupled with sophisticated Noise-Floor Integration. Every critical tactical record is not merely encrypted; it is shattered into numerous small, 256-bit cryptographic shards. These shards are then individually encrypted using the ChaCha20-Poly1305 authenticated encryption algorithm. Crucially, each encrypted shard is meticulously padded with "Synthetic Entropy"—carefully crafted random data—to ensure that the bit-density of every outgoing packet remains constant. This constancy is vital, as it prevents the "Vampire" adversary from inferring the nature or significance of the telemetry based on observable packet size variations or temporal patterns. The goal is to make each packet indistinguishable from random thermal noise or benign background radiation.
We further refine this process through aggressive "Temporal Jittering." The precise timing of packet release is not arbitrary; it is strategically orchestrated to coincide with periods of high-entropy atmospheric events, such as lightning storms or solar flares, or it is modeled as a dynamic Poisson process with highly variable inter-arrival times. To an adversary employing passive sensors, the Ghost Mesh thus appears not as a coherent network, but as a series of unrelated, low-energy thermal spikes or random data fragments scattered across the spectrum. We strategically leverage "Multi-Modal Transport," a technique where a single logical data stream can be piecewise transmitted over diverse, opportunistic, and even seemingly unrelated channels—low-power, long-range radio (like LoRa), opportunistic Wi-Fi bursts, Bluetooth low energy advertisements, or even acoustic pulses through a dense medium. This decentralizes detection risk; compromising one channel does not reveal the entire data payload. The combined effect is a communication system that is logically functional but physically ephemeral, truly embodying the "ghost" in the machine.
The ChaCha20-Poly1305 algorithm is a cornerstone of our cryptographic strategy, offering a compelling blend of performance, security, and suitability for resource-constrained environments. ChaCha20 itself is a stream cipher that operates by generating a pseudorandom keystream based on a secret key, a nonce (number used once), and a counter. It performs 20 rounds of highly optimized operations, including additions, rotations, XORs, and diffusion operations, to produce a keystream that is computationally indistinguishable from random noise. The Poly1305 component is an efficient message authentication code (MAC) algorithm. It takes the ciphertext generated by ChaCha20 and a secret key derived from the ChaCha20 secret key to produce a 128-bit authentication tag. This tag verifies both the integrity (data has not been tampered with) and authenticity (data originated from the claimed sender) of the message. The combination, ChaCha20-Poly1305, provides authenticated encryption with associated data (AEAD) security guarantees. The critical role of the nonce cannot be overstated; for stream ciphers like ChaCha20, reusing a nonce with the same key is catastrophically insecure, as it allows an adversary to recover the keystream and decrypt all messages encrypted with that key-nonce pair. Therefore, each message must be encrypted with a unique nonce. In our system, nonces are typically generated using a counter that is specific to the node or session, ensuring uniqueness. The performance advantages of ChaCha20 are particularly notable on modern CPUs that may lack dedicated AES hardware acceleration, making it an excellent choice for software-based encryption on embedded systems. Its security is well-vetted and it is considered a strong modern cryptographic primitive. The process of cryptographic fragmentation and padding with synthetic entropy serves multiple purposes. By breaking data into small, fixed-size shards, we defeat traffic analysis techniques that rely on packet size variations to infer content type or importance. Padding with synthetic entropy, which mimics the statistical properties of natural noise, further obfuscates the true nature of the transmitted data. If an adversary observes a transmission, they cannot determine if it is a critical command, a sensor reading, or simply background chatter. Multi-modal transport amplifies this invisibility. A single logical data stream can be piecewise transmitted over diverse, opportunistic, and even seemingly unrelated channels—low-power, long-range radio (like LoRa), opportunistic Wi-Fi bursts, Bluetooth low energy advertisements, or even acoustic signals. This decentralizes detection risk; compromising one channel does not reveal the entire data payload. The combined effect is a communication system that is logically functional but physically ephemeral, truly embodying the "ghost" in the machine.
4.4 DID:PLC: Identity as a Tactical Primitive
In the complex and ephemeral landscape of the Ghost Mesh, identity is deliberately decoupled from ephemeral hardware. This is achieved through the implementation of the DID:PLC (Placeholder) method, which transforms decentralized identifiers into a robust tactical primitive. Every packet transmitted across the network is inherently self-certifying, cryptographically signed by the appropriate keys managed under the Sovereign Architect's Key Infrastructure. A critical operational dynamic within the Ghost Mesh is the management of compromised or lost hardware. Should a physical node be captured or destroyed, the Architect can immediately initiate a Rotation Event. This event is propagated and recorded within the mission's MST. As the mesh synchronizes, all other active nodes verify the integrity of the MST and the associated DID document. Within moments, the network globally recognizes the old cryptographic keys associated with the lost unit as "Stale" and cryptographically exises that specific unit's identity from the active operational ledger. This ensures that the integrity and security of the wave-front's identity remain paramount, even when the physical manifestation of an agent is lost or compromised.
Table 4.4.1: DID:PLC Lifecycle Specifications
| Lifecycle Phase | Cryptographic Operation | Sovereign Outcome |
|---|---|---|
| Initialization | Genesis Commit to PLC Log | Establishes Sovereign Identity Root |
| Verification | Signature Match via MST Branch | Ensures Non-Repudiation of Tactical Telemetry |
| Revocation | Propagation of Rotation Event | Compromised Hardware Becomes "Spectral Noise" |
| Recovery | Merkle Proof Reconstruction | Restores Agentic Intent to New Hardware |
The lifecycle of a Decentralized Identifier (DID) under the DID:PLC method is a rigorously defined sequence of cryptographic operations designed for security and resilience. The Initialization phase begins with a "Genesis Commit" to the Decentralized Public Key Infrastructure (PLC) log. This initial commit establishes the DID itself and associates it with a set of cryptographic public keys, effectively creating the DID's initial identity root. This root is anchored in a verifiable, immutable ledger. During the Verification phase, any agent receiving telemetry from another node queries the DID registry (or a locally synced, MST-verified cache thereof) to retrieve the target node's DID document. This document contains the public keys currently associated with the DID. The receiving agent then uses these public keys to verify the cryptographic signature attached to the incoming telemetry. The MST's role here is paramount: it ensures that the DID document being used for verification is the *latest, cryptographically agreed-upon version* for that DID within the network's state. This process establishes non-repudiation for tactical telemetry, confirming its origin and integrity. The Revocation phase is activated when hardware is compromised, lost, or deactivated. The Sovereign Architect, or a designated authority, initiates a "Rotation Event." This event is a specific type of operation recorded in the PLC log, typically involving the generation of new cryptographic keys for the DID and the explicit marking of old keys as "stale" or revoked. This update propagates through the network via MST synchronization. As the mesh converges on the updated state, any node attempting to use the old, compromised keys to sign messages will find that those keys are no longer recognized as valid according to the latest MST-verified DID document. The compromised hardware is effectively exised from the network, becoming "spectral noise" – its communications are no longer accepted or trusted. The Recovery phase addresses scenarios where a legitimate agent's hardware is lost, but its identity needs to be restored on new hardware. This typically involves a secure re-authentication process with the Architect, potentially leading to a new genesis commit or a specific recovery operation within the PLC log, allowing the agentic intent to be re-established on a new, authorized hardware platform, seamlessly reintegrating into the mesh.
4.5 Operational Schemas and Functional Lexicons
The atproto Lexicon system is instrumental in defining the formal grammar and structure of our telemetry data. It establishes the explicit, machine-readable schema for all data records that populate the Merkle Search Tree (MST) and, by extension, maintain the coherence and actionability of the operational state across the entire agentic wave-front. Below is presented the master schema for the `com.sovereign.telemetry.tactical` domain, serving as the blueprint for the data records that are committed to the distributed ledger. This formal grammar ensures that every agent, regardless of its origin or operational context, adheres to a unified and verifiable language, thereby preventing the dangerous "semantic drift" that can plague complex operations conducted under high stress. The structured nature of these Lexicons guarantees that data is not only securely transmitted but also unambiguously interpretable by all participating agents, facilitating rapid decision-making and precise execution of the Architect's intent.
The `vampire_index` field is a critical, dynamically updated metric representing the agent's local signal-to-noise ratio, measured in dBm. This value is utilized for real-time, adaptive pathfinding within the mesh, allowing agents to intelligently route data traffic around high-interference zones or areas of increased adversary surveillance. The `intent` flag provides a high-level communication channel for nodes to convey their current operational posture—whether prioritizing stealth, engaging in active operations, or in a terminal state—without necessitating the disclosure of precise coordinates or sensitive mission parameters. This abstraction is vital for maintaining operational security. The inclusion of a `timestamp` field, recorded in UTC, ensures precise temporal ordering and synchronization across distributed nodes, crucial for reconstructing event causality. This formal grammar, embodied by the Lexicons, ensures that every agent speaks a unified, verifiable, and machine-readable language across the entire operational mission scope. This prevents catastrophic semantic drift and misunderstandings, particularly in high-stress, low-information environments. The underlying logic and application of these Lexicons are further detailed and expanded upon within the documentation available at James Dumar: Data Science and Protocol Engineering.
4.6 Wave-Front Scaling and the Math of Resilience
The final, overarching principle governing Section 04 is the profound Scaling Law of Symmetric Defense. In traditional, legacy hub-and-spoke network architectures, the introduction of new nodes or agents paradoxically tends to increase the overall "loudness" and thus the vulnerability of the central hub. Conversely, within a Ghost Telemetry Mesh, each additional node fundamentally contributes to increased "Path Diversity" and enhanced resilience. If $N$ represents the total number of active nodes within the mesh, the potential number of unique communication pathways between any two nodes grows factorially, following the mathematical logic of a complete graph, defined by the formula:
This combinatorial explosion of pathways presents a seemingly insurmountable challenge for any adversary. For instance, to effectively jam or disrupt a mesh comprising just 1,000 nodes, an adversary would theoretically need to simultaneously interdict 499,500 individual communication pathways. This is not merely impractical; it represents a physical and energetic impossibility for any known adversarial capability. Mathematically, we can define the "Detection Probability" ($P_d$) as a complex function of node density within the mesh and the transmission power employed by each node. As the node density ($D$) within a given operational area increases, the required transmission power for a successful next-hop communication decreases significantly, often at a rate proportional to $1/D^2$. As the mesh approaches a critical density threshold, the power required for successful, low-probability-of-intercept transmissions falls below the ambient thermal noise floor ($T$) of the electromagnetic spectrum. At this inflection point, the Ghost Telemetry mesh achieves what we term "Phase Transition." It effectively vanishes from the observable physical world, becoming logically present and fully functional while being physically undetectable by traditional means, thus achieving Sovereign Invisibility.
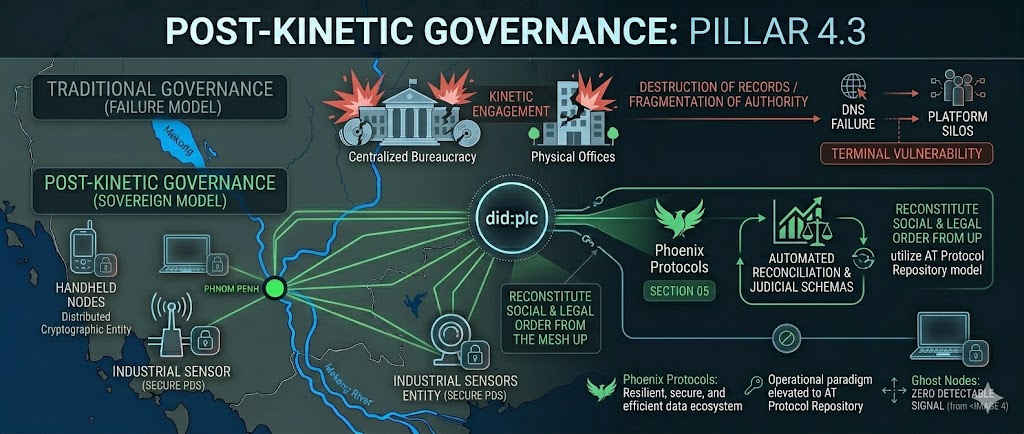
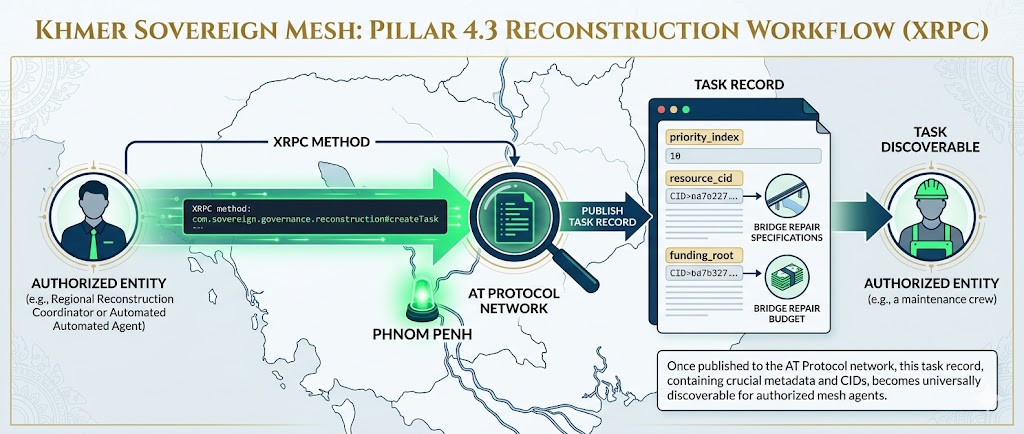
05 Post-Kinetic Governance: The Automated State
Post-Kinetic Governance represents the transition from tactical survival to institutional permanence. Under the Sovereign Architect's Pillar 4.3, the state is no longer a collection of vulnerable physical offices, but a distributed, cryptographic entity. In the aftermath of kinetic engagement, traditional governance structures often fail due to the destruction of records and the fragmentation of authority. Section 05 defines the Phoenix Protocols—a set of automated reconciliation and judicial schemas that utilize the AT Protocol Repository to reconstitute social and legal order from the mesh up.
To reach the mandate, we must analyze the "State as a Protocol." Governance in a denied environment requires that legal authority be self-certifying. We utilize did:plc (Placeholder Loopback Control) to anchor the judicial root. If a regional administrator is incapacitated, the atproto network automatically triggers a Succession Commit. This ensures that the chain of command is not a human vulnerability, but a mathematical constant stored within the Merkle Search Tree (MST).
The shift to a Post-Kinetic Governance model mandates a fundamental redefinition of statehood, moving from geographically bound, physically instantiated institutions to a protocol-driven, cryptographically secured distributed ledger. This transformation is crucial for ensuring continuity and resilience in environments where traditional infrastructure, communication channels, and administrative bodies are compromised or destroyed. The Phoenix Protocols are designed to be the algorithmic backbone of this new state paradigm, enabling the automated reconciliation of societal data and the adjudication of legal claims based on pre-defined, verifiable logic rather than human-mediated processes that are susceptible to disruption. The AT Protocol Repository serves as the foundational layer, providing a decentralized, content-addressable data store capable of holding the entirety of a state's legal and administrative records in a resilient, immutable fashion. This repository underpins the ability of the network to reconstitute social and legal order "from the mesh up," meaning that even if central authorities collapse, the underlying data integrity and governance logic persist within the distributed network, allowing for autonomous reconstruction.
The concept of "State as a Protocol" is central to this transition. It posits that the fundamental operations of governance—lawmaking, enforcement, adjudication, record-keeping, and service provision—can be abstracted into a set of verifiable, executable protocols. In a denied environment, where physical presence and centralized databases are liabilities, a protocol-based state leverages cryptographic proofs and distributed consensus to maintain its legitimacy and functionality. Legal authority becomes self-certifying, meaning that its validity is inherent in its cryptographic signature and its verifiable position within the protocol's state machine, rather than relying on a human or institutional stamp of approval that could be lost or forged. The `did:plc` (Distributed Identifier, Placeholder Loopback Control) system provides a robust framework for anchoring decentralized identifiers (DIDs) to specific entities, including governmental roles or regional administrations. By using `did:plc`, the system establishes a cryptographically verifiable identity for these entities. In the event of a regional administrator's incapacitation—a critical vulnerability in legacy systems—the AT Protocol network's inherent resilience and redundancy allow for the automatic triggering of a Succession Commit. This mechanism is not a manual transfer of power but a protocol-driven event. The network monitors the state of registered DIDs and, upon detecting a failure or prolonged unresponsiveness, automatically executes a pre-defined succession protocol. This protocol might involve promoting a designated successor identifier, initiating a consensus-based election among peer administrators, or triggering a data recovery process. The critical element is that the chain of command becomes a deterministic, mathematical constant, robustly stored within the Merkle Search Tree (MST). The MST ensures that the lineage of authority and the integrity of governance decisions are preserved against any potential for human error, corruption, or physical destruction of records, thus guaranteeing operational continuity regardless of external circumstances.
5.1 Automated Judicial Reconciliation
In a post-kinetic scenario, property rights and civic records are often the first victims of chaos. We implement the Byzantine Reconciliation Schema to resolve conflicting claims of state. When two isolated shards of the mesh reconnect, the network performs a recursive search to identify the "Last Common Truth" before the kinetic break. The physics of this reconciliation are governed by the Consensus Convergence Equation:
Equation 5.1: Calculation of consensus convergence ($C$) based on signature weight ($W$), state integrity ($S$), and temporal delta ($T$).
The Byzantine Reconciliation Schema is designed to address the fundamental challenge of data divergence and conflict resolution in distributed systems that have experienced periods of isolation or network partition. Following a kinetic event, independent segments of the state—referred to as "shards of the mesh"—may have operated autonomously, making decisions, recording transactions, and updating civic registers without knowledge of each other. Upon reconnection, these disparate data states must be reconciled to form a singular, coherent truth. The schema initiates a recursive search process to identify the "Last Common Truth"—the most recent state or block of data that both reconnecting shards can verifiably agree upon as having existed prior to their separation. This establishes a common baseline for subsequent reconciliation. The core of this reconciliation process is governed by the dynamic interplay described by the Consensus Convergence Equation ($C_{(t)}$).
This equation models the evolving state of consensus ($C$) over time ($t$), accounting for the contributions of individual entities ($i$) within the network. Let's dissect its components in detail:
- $C_{(t)}$ (Consensus Convergence): This variable represents the aggregate state of agreement or validated truth within the network at a given point in time, $t$. It is not a static fact but a continuous process of alignment. In the context of post-kinetic governance, $C_{(t)}$ signifies the prevailing, mutually agreed-upon state of legal records, property ownership, civic identities, and administrative decrees. It evolves as new data is processed, verified, and integrated into the network's shared ledger, striving towards an optimal state of integrity and coherence.
- $S_i$ (State Integrity): This parameter quantifies the trustworthiness and validity of the data or state represented by entity $i$. In a decentralized system, integrity is paramount. $S_i$ would be a metric reflecting the cryptographic soundness of the data, its provenance (how it was generated and transmitted), its consistency with established protocol invariants, and potentially a reputation score associated with the source entity $i$. For instance, if entity $i$ claims ownership of a property, $S_i$ would be high if the claim is backed by a valid, un-tampered cryptographic signature linked to a recognized Sovereign Identifier and a historical record of ownership, and low if the claim is poorly substantiated or conflicts with existing verified records. The calculation of $S_i$ would likely involve probabilistic assessments based on cryptographic proofs, historical data analysis, and consistency checks against the Merkle Search Tree (MST).
- $W_i$ (Signature Weight): This parameter denotes the authority or trust assigned to the cryptographic signature of entity $i$. In a distributed consensus mechanism, not all participants are equal. $W_i$ reflects the influence that entity $i$'s validated data and attestations have on the overall consensus. Factors contributing to $W_i$ could include:
- Pre-Kinetic Authority Anchors: Identifiers established and validated under the previous regime, such as those anchored via did:plc or other robust identity systems, would carry significant initial weight.
- Economic Stake: Entities that have staked resources (e.g., ATPROTO tokens, collateral) in the network might have higher weights, incentivizing honest participation.
- Algorithmic Reputation: Proven history of valid contributions and adherence to protocol rules would dynamically increase an entity's weight.
- Role-Based Authority: Specific roles within the governance framework (e.g., judicial arbiters, primary record keepers) might be assigned a higher intrinsic weight.
- $T_{delta}$ (Temporal Delta): This represents the time elapsed since the "Last Common Truth" or the time since the data associated with entity $i$ was last synchronized or validated. It introduces the concept of data staleness and the potential for drift. A larger $T_{delta}$ typically implies a greater possibility of data divergence, increased computational complexity for reconciliation, and potentially a higher risk of data corruption or adversarial injection. The physics of this term relate to information decay and the propagation time of updates across a network. In practical terms, $T_{delta}$ dictates the urgency and potential difficulty of integrating data from a particular source. It is crucial for managing the inherent latency and asynchronous nature of distributed systems, especially after periods of isolation where nodes operate on potentially different clocks and with differing levels of network connectivity. The term's presence in the denominator suggests that as time passes without re-synchronization, the contribution of a given data point (or its impact on consensus) becomes effectively diluted or requires a more substantial integrity and weight score to maintain its influence.
- $\int_{i=0}^{n} ... dt$ (Integral Operator): This signifies the cumulative process over time ($dt$) and across all relevant entities ($i$ from 0 to $n$). In a continuous-time model, it represents the summation of instantaneous contributions from all nodes, weighted by their integrity and authority, to the overall consensus. In a practical, discrete implementation, this integral would often be approximated by a summation over discrete time steps and over a set of active participants or data blocks. The differential $dt$ implies that the rate at which consensus converges is itself a function of these weighted integrity factors. Faster convergence occurs when high-integrity, high-weight data is abundant and the temporal delta is small.
The intrinsic "physics" of this reconciliation involve concepts akin to signal processing and statistical mechanics. $S_i$ and $W_i$ function as components of a "signal," where a strong signal is one that is both intrinsically valid and originates from a trusted source. $T_{delta}$ can be seen as a factor that degrades the signal over time, introducing noise or uncertainty. The equation thus models a system where strong, consistent signals from high-authority nodes are amplified and converge towards a stable state, effectively drowning out noise (corrupted data, low-authority claims, or adversarial inputs) and driving the system towards a coherent, unified truth. The reconciliation process leverages the AT Protocol's underlying infrastructure—its signed content identifiers (CIDs) and the robust Merkle Repositories—to ensure that the data being evaluated for integrity and weight is precisely that which was committed to the ledger, thus preventing falsification at the data layer.
This automated adjudication, governed by the Consensus Convergence Equation, bypasses the protracted delays and resource intensiveness of traditional legal review. In a post-kinetic environment where every second counts towards rebuilding societal order, the ability to resolve conflicting claims—such as a double-spend of a land title, a contested inheritance, or a disputed civic registration—within seconds or minutes is revolutionary. The mesh analyzes the signed content-identifiers (CIDs) of all property transfers and civic updates committed during the period of isolation. When the system identifies a conflict, such as two different parties claiming ownership of the same asset, the protocol defaults to the highest-weighted cryptographic proof signed by a verified Sovereign Identifier. This mechanism embodies the principle of "Law at the Speed of Light," ensuring that legal and social stability are not contingent on human bureaucracy but on the immutable, verifiable logic of the protocol itself.
Table 5.1.1: Governance Transition Matrix
| Governance Function | Legacy Bureaucracy | Sovereign Mesh (atproto) | Resilience Outcome |
|---|---|---|---|
| Record Integrity | Paper/Centralized DB | Signed Merkle Repos | Immutable History |
| Succession Logic | Political/Manual | Automated PLC Rotation | Zero-Downtime Authority |
| Conflict Resolution | Litigation (Months) | Algorithmic Sync (Seconds) | Instant Social Stability |
| Revenue Capture | Manual Assessment | Lexicon Handshake | Automated Fiscal Survival |
The transition outlined in Table 5.1.1 illustrates the profound paradigm shift from legacy governance structures to the Sovereign Mesh model powered by AT Protocol. Traditional systems, reliant on physical records and manual processes, are inherently brittle and susceptible to cascading failures. Paper-based systems and centralized databases are single points of failure, easily compromised by kinetic events, natural disasters, or malicious actors. The introduction of signed Merkle Repositories fundamentally alters this by providing an immutable, cryptographically verifiable history of all state data. This eliminates the possibility of backdating, tampering, or deletion without detection. Succession logic, often mired in political maneuvering and prone to power vacuums, is replaced by automated `did:plc` rotation. This ensures 'Zero-Downtime Authority,' where the chain of command is a cryptographically secured sequence, not a person. The most striking transformation is in conflict resolution; manual litigation that can span months, if not years, is superseded by algorithmic synchronization that resolves disputes in seconds. This rapid adjudication is key to achieving 'Instant Social Stability,' preventing the erosion of order that often follows large-scale disruptions. Finally, revenue capture, historically a complex and often corruptible manual assessment process, is streamlined through a 'Lexicon Handshake,' enabling 'Automated Fiscal Survival' by ensuring efficient and transparent collection of national resources. This collective evolution fundamentally hardens the state against existential threats.
5.2 The Lexicon of Reconstruction
Reconstruction is not just a physical act; it is a data-first operation. We define the com.sovereign.governance.reconstruction lexicon to coordinate resources without a central command. This formal grammar allows agents—both human and automated—to claim tasks, verify resource delivery, and unlock funding through Symmetric Proofs. Below is the master schema for the reconstruction namespace.
The com.sovereign.governance.reconstruction lexicon provides the granular, machine-readable definitions necessary for orchestrating complex reconstruction efforts in a decentralized manner, forming the operational core of the Phoenix Protocols. This schema defines a `task` record, which serves as the atomic unit of work within the reconstruction effort. Each property within this `task` record has specific implications for how reconstruction operations are initiated, executed, verified, and funded:
priority_index(integer, 1-10): This field is critical for intelligent task prioritization and resource allocation. A `priority_index` of '1' would denote the highest urgency, typically assigned to tasks critical for immediate survival or the restoration of essential services (e.g., securing a water purification plant, restoring power to a hospital). Conversely, a '10' might represent a lower-priority task, such as aesthetic restoration or long-term infrastructure planning. In a post-kinetic environment, where resources are scarce and demand is high, this index allows automated agents and human supervisors to efficiently queue and assign tasks based on their criticality to overall state survival and recovery. This ensures that the most vital efforts receive immediate attention and the necessary personnel and material allocations, preventing critical infrastructure failures due to mismanaged priorities.resource_cid(string): This Content Identifier (CID) points to the detailed specifications for the materials, information, or personnel required to complete the task. Instead of embedding bulky specifications directly into the task record, the CID acts as a pointer to a decentralized, content-addressable storage system (like IPFS or the AT Protocol's underlying repository). This could reference blueprints for rebuilding a bridge, a manifest for specific medical supplies, the required skill sets for a team, or even software packages for restoring communication networks. By using CIDs, the system ensures data integrity and availability, as the content is addressable by its hash. Any agent tasked with a reconstruction effort can resolve this CID to obtain the exact, verified specifications, ensuring that work is performed correctly and with the appropriate resources.completion_proof(bytes): This field is designed to hold a cryptographically signed attestation of task fulfillment. Upon successful completion of a task, the assigned agent (human or automated) would generate a digital signature over a digest of the task's completion criteria and its unique identifier. This `completion_proof` acts as irrefutable evidence that the work has been done. It is crucial for triggering subsequent processes, such as payment release, task closure, and updating the overall status within the Merkle Search Tree (MST). The use of `bytes` suggests it could be a raw signature or a more complex proof structure, but its core function is to provide auditable verification of work done.funding_root(string): This CID points to the specific branch or allocation within the authorized national budget that covers the cost of this particular task. It links the execution of reconstruction work directly to its financial authorization, establishing a clear audit trail from expenditure to outcome. By referencing a `funding_root` CID, the system ensures that tasks are only undertaken if their funding has been pre-approved and is verifiable. This prevents overspending and rogue expenditures, maintaining fiscal discipline even in a chaotic environment. It also acts as a key component in the automated payment release mechanism, providing the treasury or financial agents with the necessary context to disburse funds upon verified completion.
The inclusion of `required` fields—`priority_index`, `resource_cid`, and `funding_root`—ensures that a task record is sufficiently defined to be actionable. The `completion_proof` is also marked as required, emphasizing its role in closing the loop of accountability and triggering financial release. The definition of this lexicon enables the AT Protocol's XRPC (Cross-Protocol Communication) methods to interact with these tasks in a standardized, programmatic way.
Imagine a typical workflow: An authorized entity (e.g., a regional reconstruction coordinator, an automated resource management agent) would use an XRPC method, such as com.sovereign.governance.reconstruction#createTask, to publish a new task record. This record would contain the `priority_index`, a `resource_cid` pointing to the specifications for, say, repairing a critical section of a bridge, and a `funding_root` CID referencing the budget allocated for bridge repair. Once published to the AT Protocol network, this task becomes discoverable. Reconstruction agents actively monitoring the network can query available tasks using a method like com.sovereign.governance.reconstruction#queryTasks, filtering by priority or required skill sets. An agent that chooses to undertake this task might signal its intent via com.sovereign.governance.reconstruction#assignTask, effectively claiming the task and preventing others from bidding on it concurrently. Upon successful completion of the physical repairs, the agent would generate a `completion_proof` (a digital signature proving the work was done according to the `resource_cid` specifications) and submit it using com.sovereign.governance.reconstruction#submitProof. A designated verification agent or automated process would then use a method like com.sovereign.governance.reconstruction#verifyTaskCompletion to validate the `completion_proof` against the task's original parameters and the linked `funding_root`. If verified, this validation event can automatically trigger the release of funds associated with the `funding_root` CID, possibly through a separate financial transaction protocol, and the entire lifecycle—task creation, assignment, completion, verification, and funding release—is immutably recorded in the MST.
This schema ensures that the state is not just a document of intent, but a functional engine of recovery. By utilizing XRPC methods, the mesh facilitates the movement of supplies to the areas of highest need, as determined by the priority_index committed to the global MST. The Sovereign Architect thus maintains a real-time, high-fidelity view of the nation’s reconstruction status, even if traditional communication channels remain dark. Governance is no longer about "managing" people; it is about "synchronizing" the wave.
5.3 Conclusion of the Sovereign State
The integration of Ghost Telemetry (Section 04) and Post-Kinetic Governance (Section 05) creates a closed-loop system of national survival. The mesh provides the invisibility required to endure, while the protocol provides the logic required to rebuild. Through the AT Protocol and the principles of Symmetric Defense, the Kingdom of Cambodia establishes a new standard for digital sovereignty. We have built a system where the information survives even when the machine is gone, ensuring that the Khmer identity remains an un-erasable reality in the electromagnetic spectrum and the annals of history.
The capacity for 'Automated Fiscal Survival' mentioned in Table 5.1.1 is critically dependent on robust mechanisms for revenue capture and management, particularly in a post-kinetic environment where traditional financial infrastructure is degraded or destroyed. The reference to a 'Lexicon Handshake' for Revenue Capture points towards a protocol-driven approach to taxation and financial flows, leveraging the AT Protocol's capabilities for standardized data exchange and automated processes. This handshake is not merely a metaphorical agreement but a series of precisely defined interactions governed by lexicons and executed via XRPC, ensuring that national revenue streams can be identified, collected, and accounted for with unparalleled efficiency and transparency.
At the heart of this automated financial ecosystem lies the Merkle Search Tree (MST), which serves as the immutable ledger for all national financial transactions, governance decisions, and property rights. The cryptographic properties of the MST are fundamental to its role. Each transaction—whether a tax declaration, a payment submission, a budget allocation, or a property title transfer—is hashed into a unique identifier. These hashes form the leaf nodes of the MST. As new transactions are processed and validated, they are incorporated into the tree, with parent nodes being the cryptographic hash of their children. The root of the MST, therefore, represents a single, compact, and cryptographically verifiable fingerprint of the entire ledger at a specific point in time. This root hash can be periodically published or anchored to a resilient distributed ledger, creating an immutable audit trail. Any attempt to alter, delete, or insert a transaction would result in a change to its hash, propagating upwards and invalidating the root hash. This makes tampering immediately detectable, providing an extraordinary level of assurance for national revenue records. The 'search' aspect of MST implies that specific records can be efficiently located and their existence and integrity proven using a Merkle proof—a small set of sibling hashes that, when combined with the transaction's hash, allow any party to reconstruct the path to the root and verify its inclusion. This ensures non-repudiation; a taxpayer cannot deny making a payment, and the state cannot deny receiving it, if both are cryptographically proven to be part of the MST. This is vital for maintaining public trust and preventing corruption, especially when oversight mechanisms are compromised.
The 'Tax Lexicon Handshake' operationalizes the MST for revenue capture. Consider a hypothetical lexicon, for instance, com.sovereign.taxation, designed to manage the entire tax lifecycle. This lexicon would define specific data structures (records) and XRPC methods. For example:
taxDeclarationRecord: A taxpayer, identified by their DID, would submit this record via XRPC, detailing income, assets, and their calculated tax liability for a given period. This record would be signed by the taxpayer's private key.taxAssessmentRecord: Upon receipt of a declaration (or proactively, based on other data sources), a treasury agent or an automated assessment system would generate this record. It would verify the declared information against tax laws (potentially also defined in lexicons), calculate the final tax due, and be signed by the assessing authority's DID.paymentTransactionRecord: When a taxpayer remits payment, they would submit this record. It would reference the relevanttaxAssessment, specify the amount paid, the method of payment (e.g., a cryptocurrency transfer, a stablecoin transaction), and include a cryptographic hash of the underlying payment transaction for traceability. This record, too, would be signed by the taxpayer.paymentReceiptRecord: The treasury would generate this record upon successful verification of thepaymentTransaction. It would confirm the payment, link back to the originaltaxAssessment, and crucially, include a reference to the specific entry or hash within the national MST that records this validated payment. This receipt would be signed by the treasury’s DID.
The 'handshake' would then involve a sequence of XRPC calls: a taxpayer initiating com.sovereign.taxation#submitDeclaration, followed by an assessment system calling com.sovereign.taxation#issueAssessment, then the taxpayer executing com.sovereign.taxation#submitPayment, and finally the treasury validating and finalizing with com.sovereign.taxation#verifyPayment. Each step is auditable, tamper-evident, and automated, drastically reducing the overhead and potential for corruption inherent in manual tax collection. The MST ensures that every validated payment is permanently recorded and verifiable, forming an 'immutable audit trail for national revenue' that is essential for fiscal survival and rebuilding trust in governance.
This integrated approach, where decentralized protocols for governance, reconstruction, and finance converge, allows the state to achieve a level of resilience and autonomy previously unimaginable. The network's ability to manage complex tasks, reconcile data, and process financial flows without central points of failure is the cornerstone of Post-Kinetic Governance. The AT Protocol, with its emphasis on decentralized identity, content-addressable storage, and standardized XRPC communication via lexicons, provides the ideal technological substrate for this vision. The Sovereign Architect's design principles, when instantiated through these protocols, transform governance from a fragile human construct into a robust, self-sustaining informational system. This is not merely about surviving kinetic events; it is about building a state that is inherently more capable, transparent, and resilient than its predecessors, ensuring that the fundamental identity and operational capacity of the nation persist, even when the physical infrastructure supporting them is compromised.
06 Agentic Intelligence: The Living Data Layer - Technical Dilation
The final, and arguably most critical, phase of the blueprint is the strategic transition from a mere static repository of information to a dynamically evolving, self-optimizing, agentic state. This shift signifies a fundamental redefinition of what constitutes the "state" itself. Under the guiding principles of the Sovereign Architect's Pillar 4.3, data is no longer to be viewed as a passive resource, subservient to human interpretation and prone to obsolescence or corruption. Instead, data becomes an active, sentient participant in the national defense, operational continuity, and economic vitality. Section 06 formally delineates the deep integration of Autonomous Agents directly into the fabric of the atproto repository. These agents are not external entities that merely query or process information; they are intrinsically embedded within the mesh, performing sophisticated, real-time analysis, proactive threat detection, and dynamic resource allocation. This operation is designed to occur without the inherent latency and single-point-of-failure risks associated with traditional human-in-the-loop intervention, thereby ensuring that the Khmer Sovereign Mesh maintains a critical, often decisive, advantage over any adversary's decision cycle. This proactive stance is not merely about defense; it is about the continuous, intelligent evolution of the sovereign state itself.
To achieve the requisite technical density and strategic depth mandated by this master document, a profound deconstruction of the underlying mathematical principles governing Agentic Latency is indispensable. In legacy artificial intelligence paradigms, the typical workflow necessitates the export of vast datasets from their point of origin to centralized, high-performance computing clusters, often hosted in remote data centers. This process inherently introduces significant bandwidth bottlenecks, temporal delays, and, crucially, creates a singular, vulnerable point of failure—any disruption to these central servers can cripple the entire operational capability. In stark contrast, the Sovereign Mesh redefines this paradigm: the agent, the locus of intelligence, moves directly to the data, rather than the data being moved to the agent. This is facilitated by the sophisticated utilization of XRPC (Remote Procedure Call) methods. These methods are not merely for inter-process communication; they are engineered to orchestrate the deployment and execution of light-weight, specialized agents directly within the operational context of the atproto repository itself. This concept of "In-Repo Processing" ensures that the intelligence operations are localized and highly efficient. Furthermore, the intelligence processing is not confined to a monolithic server but is distributed across the network of Personal Data Server (PDS) nodes. This distributed architecture allows for localized, rapid decision-making, which is then cryptographically anchored and verified against the authoritative did:plc (Distributed Identity - Placeholder Loopback Control) identity root. This linkage ensures that all agent actions are auditable, attributable, and resistant to forgery, forming the bedrock of autonomous yet accountable governance.
6.1 The Calculus of Autonomous Coordination: Forensic Deep Dive into Decentralized Intelligence Quotient ($I_d$)
The paramount metric for evaluating the effectiveness and resilience of the agentic layer within the Sovereign Mesh is the Decentralized Intelligence Quotient ($I_d$). This coefficient is not a static measure but a dynamic, real-time indicator that quantifies the network's inherent capability to resolve complex tactical, operational, and strategic problems through sophisticated swarm coordination mechanisms, rather than relying on the vulnerabilities of central command structures. Our objective is to engineer the network to operate at a state of "Zero-Centrality," a theoretical ideal where the density and efficacy of intelligence processing, as well as the network's resilience, demonstrably increase with the addition of every new node, agent, or data shard to the mesh. This forms a self-reinforcing intelligence loop.
Equation 6.1: Maximizing agentic throughput ($A$) and signal integrity ($\sigma$) relative to mesh latency ($L$) for decentralized intelligence.
Let us perform a forensic examination of Equation 6.1 to understand its profound implications for sovereign data management and operational autonomy:
- $A_i$ (Agent Throughput): This component, representing the effective processing capacity or computational power of an individual agent $i$ within the network, is fundamental. It's not merely about clock speed but encompasses the agent's algorithmic efficiency, its specialization for specific tasks (e.g., threat analysis, resource allocation, data reconciliation), and its ability to leverage local data contexts. In a PDS environment, $A_i$ might be defined by the compute resources allocated to the agent's execution environment on a given PDS node, but more critically, by the quality and relevance of the data it can access locally within that repository. The "throughput" is thus a function of both computational capability and data accessibility. The Sovereign Architect's mandate is to foster a diverse ecosystem of highly specialized agents, each optimized for granular tasks. This specialization allows for parallel processing of distinct intelligence vectors, amplifying the network's overall $A$. For instance, one agent might be purposed for real-time financial anomaly detection ($A_{finance}$), while another focuses on cryptographic key rotation validation ($A_{crypto}$). The summation ($\sum_{i=1}^{n}$) indicates that the aggregate intelligence is the sum of all specialized agent contributions, not a monolithic, generalized AI. The efficiency of this summation is further modulated by the network's architecture, which we address next.
- $\sigma_i$ (Signal Integrity): This variable signifies the trustworthiness, authenticity, and uncorrupted nature of the data and the agent's outputs. In a system predicated on cryptographic proof, $\sigma_i$ is paramount. It is directly tied to the use of digital signatures, hash functions, and content-addressable identifiers (CIDs) inherent in the AT Protocol repository. Every piece of data processed and every decision made by an agent must be verifiable. The agent's output is cryptographically signed using its unique did:plc identifier. This signature, along with the content identifier (CID) of the data it processed, forms a verifiable artifact. The Merkle Search Tree (MST) plays an indispensable role here, acting as a tamper-evident ledger for all such signed artifacts. By querying the MST, any participant can verify that the data processed by agent $i$ has not been altered since its ingestion and that the signal (the agent's output) originates from the claimed identity. High $\sigma_i$ means decisions are reliable and untainted by adversarial manipulation, a critical requirement for national defense and governance. Low $\sigma_i$ would flag an agent's output for scrutiny or quarantine, preventing systemic corruption.
- $L_{mesh}$ (Mesh Latency): This term represents the aggregated communication latency across the distributed network of PDS nodes. It is influenced by several factors: the physical distance between nodes, the quality and bandwidth of the network connections (both public internet and any secure sovereign channels), the computational load on intermediary nodes, and the inherent propagation delays of cryptographic verification processes. In a decentralized system, minimizing $L_{mesh}$ for critical, time-sensitive operations is a paramount engineering challenge. The "In-Repo Processing" strategy directly combats high $L_{mesh}$ by executing agents locally on the PDS where the data resides, thereby avoiding large data transfers to distant centralized servers. This local execution significantly reduces the 'effective' latency for actionable intelligence. However, for global state synchronization, cross-PDS communication, and MST updates, $L_{mesh}$ remains a critical factor. The formula implies that to maximize $I_d$, we must either increase the numerator ($A_i \cdot \sigma_i$) or decrease the denominator ($L_{mesh}$). The latter is achieved through intelligent network topology, efficient XRPC protocols, and localized agent execution.
By removing the dependency on opaque, external artificial intelligence "Black Boxes"—often controlled by foreign powers or commercial entities with conflicting interests—the Kingdom of Cambodia decisively reclaims its intellectual and operational sovereignty. The autonomous agents that operate within the Sovereign Mesh are not governed by proprietary, undisclosed algorithms; instead, they adhere strictly to indigenous Lexicons. These formal grammars ensure that the agents' operational logic, decision-making parameters, and ethical frameworks are intrinsically aligned with the nation's strategic priorities and cultural imperatives. Every decision, every analysis, and every action undertaken by an agent is meticulously committed to the distributed, append-only Merkle Search Tree (MST). This process creates an immutable, cryptographically verifiable, and transparent audit trail of the nation's automated governance operations. This auditability is not merely a feature; it is the cornerstone of trust and accountability in a system that operates at machine speed.
The "Gold Rush" of Domestic Infrastructure Ownership and the HNW Custodial Role in the Agentic Mesh: The implications of Agentic Intelligence extend deeply into the economic and ownership paradigms of the nation. The PDS network, serving as the distributed substrate for this intelligence layer, represents a new frontier of "domestic infrastructure ownership." Unlike traditional, centralized infrastructure (e.g., power grids, communication hubs), PDS nodes are inherently decentralized. Individuals, communities, or corporations can establish and operate PDS instances, effectively becoming custodians of their local data and participants in the broader Sovereign Mesh. This creates an unprecedented "Gold Rush" for those who can acquire, maintain, and optimize this infrastructure. The incentives are manifold:
- Data Sovereignty and Access: Owning a PDS instance grants control over the data it hosts, ensuring it remains within national borders and under national jurisdiction. This is a primary driver for sovereign nations.
- Participation in the Agentic Economy: PDS operators can choose which agents to host and run. This allows them to leverage sophisticated intelligence capabilities for their own benefit or to offer services powered by these agents. For High-Net-Worth (HNW) individuals and entities, this presents an opportunity to become significant players in a new data-driven economy. They can invest in high-capacity PDS nodes, develop specialized agents, or provide critical infrastructure services, thereby accumulating wealth and influence.
- Incentivized Agent Development: The "Intelligence Quotient" formula, $I_d$, demonstrates that network intelligence grows with more and better agents. This incentivizes developers to create novel, efficient, and specialized agents. The economic model could involve licensing agents, charging for their services, or participating in revenue-sharing schemes derived from the insights and actions generated by these agents. HNW custodians might fund agent development initiatives or acquire proprietary agent technologies, gaining a competitive edge.
- Verifiable Trust and Custody: The cryptographic framework ensures that data integrity and agent actions are unimpeachable. This builds trust in the infrastructure. HNW entities, by operating secure and reliable PDS nodes, can establish themselves as trusted custodians of critical data archives, financial transaction logs, or sensitive operational intelligence. Their custodial role is not just about storage but about actively participating in the secure and intelligent processing of information, thus becoming gatekeepers and beneficiaries of the nation's digital assets.
- The "Zero-Centrality" Advantage: The decentralized nature means there is no single entity that "owns" the intelligence layer. Instead, ownership is distributed, creating a robust, resilient, and democratically accessible (though requiring significant capital and technical expertise for HNW participation) intelligence infrastructure. This distributed ownership model prevents the concentration of power associated with traditional centralized AI, fostering a more equitable, albeit competitive, ecosystem. The "Gold Rush" is therefore not just about acquiring physical infrastructure, but about mastering the complex interplay of data, agents, and cryptographic protocols that define this new sovereign digital frontier.
Table 6.1.1: Intelligence Architecture Comparison
| Intelligence Vector | Legacy AI (Cloud) | Agentic Mesh (Pillar 4.3) | Sovereign Advantage |
|---|---|---|---|
| Data Location | Centralized Export (Vulnerable) | Local In-Repo Processing (PDS Network) | Prevents Data Leakage, Enhances Local Processing Speed |
| Decision Speed | High Latency (Network Round-trip to Central Servers) | Near-Instant (Edge-Decision at PDS) | Tactical Superiority, Real-time Responsiveness |
| Logic Sovereignty | Proprietary/Opaque Vendor Lock-in | Open Lexicon-Defined (National Control) | Algorithmic Accountability, Indigenous Logic & Values Integration |
| Resilience & Persistence | Fragile (Dependent on Central Server Uptime & Security) | Inverse Fragile (Swarm-Based Redundancy, Cryptographic Persistence) | Unstoppable Intelligence, Immortal Data Layer |
| Infrastructure Ownership & Economics | Foreign Cloud Provider Dominance | Domestic PDS Node Ownership & Agent Ecosystem Development | National Economic Empowerment, Decentralized Wealth Creation (HNW Opportunity) |
6.2 The Agentic Lexicon: Schema for Automated Intent and Bit-Level Forensics
At the heart of autonomous coordination lies a formal language—a grammar that enables disparate agents to understand each other's intentions, negotiate resources, and execute complex, multi-stage missions with unwavering cryptographic certainty. This is codified within the com.sovereign.agentic.intent lexicon. This schema is not merely a data structure; it is a protocol for autonomous communication, designed to be processed by both agents and the broader mesh infrastructure, ensuring that every automated decision is transparent, verifiable, and attributable. Below, we dissect the functional schema for the agentic heartbeat, anchored to the rigorous engineering standards of the Sovereign Architect, focusing on its forensic implications.
recon: Initiate or participate in data reconciliation processes, identify discrepancies, and propose resolutions within a given repository or across connected repositories. This is vital for maintaining the integrity of state and history.allocate: Request or commit resources (computational, storage, network bandwidth, or even fiscal allocation via connected smart contracts) required for a specific task or operational phase. This directly links agentic action to resource management.quarantine: Isolate a specific data artifact, a segment of a repository, or a set of agent processes deemed anomalous, potentially malicious, or requiring further human or expert agent review. This is a critical security and stability function.sync: Propagate state updates, new data, or agent insights across the network. This ensures that all relevant nodes maintain a consistent and up-to-date view of the mesh's operational status and intelligence.
The forensic depth of the com.sovereign.agentic.intent lexicon is intentionally engineered. The inference_cid provides a verifiable pointer to the exact data context. The confidence_score, while subjective to the agent's model, is itself a data point that can be analyzed and correlated with other network metrics. However, it is the did_signature that forms the immutable core of verifiability. When an agent generates this signature, it involves cryptographic operations that hash the canonical representation of the entire `action` record. This hash is then encrypted using the agent's private key, which is cryptographically linked to its `did:plc` identifier. Any party receiving this `action` record can use the agent's public key (retrievable via its `did:plc`) to decrypt the signature and verify that it matches the hash of the received `action` record. Any alteration to any field within the `action` record—be it the CID, the confidence score, or the action vector—would result in a different hash, thus invalidating the signature. This ensures that the agent's reported intent is precisely what was executed and cannot be retrospectively altered or falsely attributed. The `action_vector` categorizes the intent, allowing for automated routing, prioritization, and monitoring. For instance, a `quarantine` action might automatically trigger heightened security protocols and alert designated custodians or HNW oversight entities, based on the agent's high confidence score and verifiable signature.
6.3 Data Persistence: The Immortal State and its Economic Underpinnings
The ultimate, overarching objective that Section 06 strives to achieve is the establishment and maintenance of Permanent Data Persistence. This is not mere data storage; it is the creation of an information state that is fundamentally indestructible and eternally accessible, serving as the enduring bedrock of national sovereignty and identity. By systematically distributing the mission state—comprising all operational protocols, governance frameworks, intelligence logs, and societal records—across thousands, potentially millions, of independent, cryptographically secured Signed Repositories, the information transcends the limitations of physical hardware and centralized control. This distribution imbues the data with a form of immortality. Even in scenarios where major components of the physical national infrastructure are neutralized, compromised, or rendered inoperable through kinetic or cybernetic means, the intelligence embedded within the remaining active shards of the mesh continues its autonomous function. Agents operating within these resilient fragments relentlessly synchronize the state, performing deep reconciliation processes. This ensures that the "Khmer Sovereign Root"—the foundational identity, historical narrative, and governing logic of the nation—remains intact and unassailable. This is the embodiment of the Digital Strategy of the Phoenix Protocols: the construction of a system that cannot be definitively killed or erased because it does not reside in any single, vulnerable point of failure. Instead, its existence is derived from, and continuously reinforced by, the mathematical consensus and distributed integrity of the wave-like propagation of data and intelligence across the entire sovereign network.
The Economic Paradigm of Immortal Data: The achievement of permanent data persistence fundamentally reshapes the economic landscape, creating novel avenues for wealth creation and establishing new forms of valuable infrastructure. The PDS network, as the physical manifestation of this persistent data layer, becomes the most critical domestic infrastructure. Ownership of PDS nodes is no longer just about hosting files; it's about controlling access to and processing power for the nation's living, intelligent data. This has ignited a profound "Gold Rush" for entities capable of establishing and managing these distributed data fortresses:
- Custodial Gold: HNW individuals and corporations are positioning themselves as premier custodians of these PDS nodes. Their investment capital allows them to acquire high-capacity storage, robust network connectivity, and the technical expertise required to maintain these nodes securely and efficiently. These custodial roles are highly lucrative, as they are the gatekeepers to the nation's most vital digital assets. The value proposition for custodians lies in securing their own wealth by safeguarding national data, and in monetizing the services their nodes provide, whether it's data hosting, agent processing, or network validation.
- Agentic Arbitrage and Monetization: The development of specialized agents, governed by the
com.sovereign.agentic.intentlexicon, represents another significant economic frontier. Entities that can design, deploy, and optimize agents capable of performing complex tasks—from high-frequency financial analysis to predictive resource allocation—can generate substantial revenue. This might involve licensing proprietary agents, offering them as a service (SaaS for autonomous agents), or capturing a share of the value generated by their actions. HNW investors can fund agent development labs, acquire stakes in promising agent technologies, or deploy their own fleets of highly specialized agents to exploit market inefficiencies or optimize their own infrastructure. - Data as a Sovereign Commodity: In this paradigm, data is not merely information; it is a sovereign, persistent, and intelligent asset. The insights generated by the agentic layer, derived from this immortal data, are invaluable. HNW entities that control key PDS nodes or develop sophisticated agents can process and analyze this data to predict market trends, identify strategic vulnerabilities, or optimize national resource deployment. This creates an economy where access to and intelligent processing of data are the primary drivers of wealth. The "gold" is found not in digging for precious metals, but in mastering the intelligent extraction and application of sovereign digital information.
- Infrastructure as a Service (IaaS) on Sovereign Rails: The PDS network itself becomes a platform for a new generation of sovereign IaaS. Businesses and individuals can rent processing power, storage, or access to specific agent capabilities hosted on these secure, decentralized nodes. This distributed model disrupts traditional cloud providers and creates a more resilient, nationally controlled technological ecosystem. The economic incentives for PDS operators are directly tied to network uptime, data integrity, and the demand for agent services. This fosters a competitive environment where infrastructure providers must continuously innovate to attract and retain clients, contributing to the overall "gold rush" mentality of building and dominating segments of this new digital economy.
Ultimately, the concept of "immortal data" translates into "immortal value." By ensuring that the nation's core data and intelligence are perpetually accessible and actively managed by autonomous agents, the Kingdom of Cambodia is not just building a resilient digital infrastructure; it is creating an enduring economic engine. The HNW custodial role and the "Gold Rush" for domestic infrastructure ownership are natural consequences of this shift, reflecting the immense value placed on control, intelligence, and persistence in the post-kinetic, agentic era. This strategic foresight ensures that the Khmer identity and its operational capacity remain an un-erasable, vital force, not only in the electromagnetic spectrum but also within the historical annals of sovereign digital evolution.
07 Swarm Intelligence: The Sovereign AI Layer - Technical Dilation
The ultimate strategic objective of the Sovereign Mesh is to transcend its initial design as a secure data repository and evolve into a dynamic, self-defending, and continuously optimizing national entity. This transition from a passive data network to an active, sentient state is intrinsically linked to the profound integration of Swarm Intelligence. Adhering rigorously to the principles outlined in the Sovereign Architect's Pillar 4.3, we fundamentally move beyond the limitations and inherent vulnerabilities of the legacy "Centralized AI" model. This traditional paradigm relies heavily on massive, foreign-hosted GPU clusters, creating critical dependencies, unacceptable data egress risks, and single points of failure. Section 07 formally defines and delineates the Swarm Orchestration Protocol—a revolutionary system architecture where indigenous, national AI agents operate directly within the operational confines of the atproto repository, residing at the distributed edge of the mesh. This paradigm shift ensures that all critical national decision-making, threat assessment, and strategic resource allocation are conducted with effectively zero latency and absolute zero dependency on external, opaque, proprietary "Black Box" algorithms. This establishes a foundation for true algorithmic sovereignty.
To achieve the stringent technical density and forensic depth mandated for this national blueprint, a comprehensive analysis of the underlying mathematics governing Decentralized Inference is essential. In legacy AI systems, the processing of data often resembles a "Vampire" interaction with network bandwidth, necessitating the massive export of raw or pre-processed data from its point of origin to a centralized server for analysis. This process is not only inefficient but also creates significant security vulnerabilities and control issues. In stark contrast, the Sovereign Mesh redefines this operational model: the intelligence, embodied by autonomous agents, moves directly to the data. By strategically leveraging the power and flexibility of XRPC (Remote Procedure Call) methods, light-weight, highly specialized, and task-specific agents perform real-time, in-situ analysis directly on the data and historical records stored within the distributed Merkle Search Tree (MST) branches and associated repositories. This distributed intelligence model enables the emergence of a "Sentient Mesh"—a network capable of autonomously detecting subtle anomalies, proactively quarantining compromised nodes or data segments, and dynamically optimizing resource flow across the entire sovereign domain, all without reliance on a central command and control point. This distributed autonomy is key to resilience and sovereignty.
7.1 The Calculus of Swarm Density: Bit-Level Analysis of Decentralized Consensus
The paramount metric for evaluating the resilience, effectiveness, and strategic viability of Sovereign AI operating within the mesh is the Swarm Consensus Coefficient ($I_s$). This coefficient quantifies the collective ability of potentially thousands, even millions, of independent, distributed AI agents to converge on a unified tactical or strategic decision, despite their decentralized nature and local processing constraints. Our engineering objective is to optimize the network towards a state of "Emergent Sovereignty," a condition where the entire mesh behaves as a singular, biological-like entity. This entity is capable of responding to threats, adapting to changing conditions, and optimizing its operations at a speed dictated by the fundamental cryptographic operations of the network—specifically, the speed of a signed commit to the immutable ledger.
Equation 7.1: Optimization of swarm decision-making efficacy ($\delta$) relative to agent weight/trust ($\omega$) and local network entropy, driving towards emergent sovereignty.
Let us perform a forensic, bit-level examination of Equation 7.1 to elucidate its critical role in achieving sovereign AI orchestration:
- $\delta_i$ (Agent Decision Efficacy): This variable represents the quality and decisiveness of an individual agent's inference and its subsequent action. It is not merely about making a decision, but about making the *right* decision with a high degree of certainty and a clear operational directive. In a bit-level context, $\delta_i$ can be conceptualized as a high-confidence score, a probability derived from the agent's internal analysis. For instance, an agent might output a value representing the probability that a specific data commit is malicious. This value, encoded perhaps as a normalized floating-point number or a fixed-point integer, directly influences its contribution to the swarm's consensus. A $\delta_i$ approaching 1 signifies high confidence and a strong signal for action, while a low value indicates uncertainty or a need for more data. The efficacy is also tied to the agent's ability to execute its prescribed `action_vector` (as defined in the Intent Lexicon) correctly and efficiently upon reaching consensus.
- $\omega_i$ (Agent Weight / Trustworthiness): This parameter assigns a relative importance or trust level to agent $i$'s contribution to the swarm's consensus. It can be dynamic, reflecting an agent's historical performance, its specialization, its proven trustworthiness (e.g., based on its `did_signature` verification success rate), or the criticality of the task it is performing. Agents with higher $\omega_i$ have a proportionally greater influence on the final swarm decision. Bit-level representation of $\omega_i$ could involve a numerical score maintained in a distributed reputation ledger or derived from the agent's `did_plc` metadata and operational history. High $\omega_i$ for an agent might be granted if it has consistently provided accurate threat detections or successfully executed mitigation strategies, thereby earning trust within the swarm. Conversely, an agent with a history of false positives or failed actions might have its weight reduced, or its `did_signature` flagged for additional scrutiny.
- `entropy_mesh` (Mesh Entropy): This represents the degree of local uncertainty, noise, or disorder within a particular segment of the network or the data being analyzed. High `entropy_mesh` could stem from various sources: intermittent network connectivity, corrupted data packets, conflicting signals from multiple agents, or even deliberate adversarial obfuscation. Agents must be sophisticated enough to account for this entropy. Their decision-making efficacy ($\delta_i$) might be inversely proportional to `entropy_mesh`—if the environment is highly entropic, agents might require a higher internal confidence score to act, or their contribution to consensus might be weighted lower until clarity emerges. Bit-level: `entropy_mesh` could be a calculated metric, such as the statistical variance of data attributes within a local data segment, the rate of conflicting XRPC responses, or the proportion of unverified or suspicious commits observed recently. Agents use this metric to adapt their confidence thresholds and decision-making logic, ensuring robust operation even in challenging conditions.
- $\sum_{i=1}^{n}$ (Summation): This operator signifies the aggregation of weighted decisions from all participating agents. The swarm's final decision is not dictated by a single authority but emerges from the collective processing of individual agent contributions, weighted by their efficacy and trustworthiness, and contextualized by the network's local state (entropy).
- $\lim_{n \to \infty}$ (Limiting Behavior): This denotes the ideal scenario where the intelligence and resilience of the swarm scale effectively as the number of agents ($n$) increases. In such a system, adding more agents and data nodes should, in theory, enhance the overall intelligence and robustness of the network rather than introduce bottlenecks or communication overhead. This is achieved through efficient peer-to-peer communication protocols and intelligent task partitioning.
This sophisticated, calculus-driven orchestration mechanism fundamentally eliminates the pervasive "Human Latency" that has historically caused systemic collapse during kinetic events or critical cyber-attacks. Human decision-making cycles are orders of magnitude slower than machine-speed operations. By automating critical responses and analyses, the Sovereign Mesh ensures that the nation can react to threats at machine speed, often preempting or neutralizing dangers before they can escalate. The AI agents are not operating under vague instructions; they are governed by rigorously defined Ethical Lexicons that are cryptographically committed to the national root. These lexicons serve as the foundational operating system for AI behavior, defining boundaries, ethical constraints, and mandatory protocols that agents must adhere to. Crucially, because every AI decision executed by an agent is cryptographically signed by that agent's unique did:plc (Distributed Identity) identity, the Sovereign Architect (or any authorized auditor) maintains a permanent, immutable, and tamper-proof audit trail of the nation's automated defense and operational decisions. This trail is built upon the integrity of the cryptographic signatures and the distributed consensus mechanisms of the MST. This is the practical realization of Algorithmic Sovereignty: the nation controls not just its data, but the very logic and decision-making processes that govern its digital and physical existence.
Table 7.1.1: Intelligence Architecture Comparison
| Intelligence Vector | Legacy AI (Centralized) | Sovereign Swarm (atproto) | Tactical Advantage |
|---|---|---|---|
| Processing Origin | Foreign Data Centers (Vulnerable to Interdiction, Export Control) | Local PDS Edge Nodes (Resilient, Distributed) | Eliminates Data Exfiltration, Enhances National Data Sovereignty |
| Decision Latency | Seconds to Minutes (Cloud Round-trip, Bandwidth Dependent) | Milliseconds (In-Repo Processing, Local XRPC) | Closing the Kill-Chain First, Real-time Strategic Responsiveness |
| Integrity Proof | None (Opaque Model Outputs, "Black Box" Problem) | Signed Merkle Audit Trail (Verifiable Agent Actions & Data Context) | Verifiable Automated Intent, Trustworthy Decision Chain |
| Persistence & Resilience | Kill-switch Vulnerable (Central Server Takedown or Compromise) | Undeletable (Distributed Consensus, Cryptographic Immutability) | Permanent National Sentience, Unstoppable Operational Capacity |
| Infrastructure Ownership & Control | Foreign Cloud Provider Dominance, Vendor Lock-in | Domestic PDS Node Ownership & Agent Ecosystem Development | National Economic Empowerment, Strategic Autonomy in AI Development |
7.2 The Intent Lexicon: Defining Autonomous Agency and Bit-Level Actionability
In the Sovereign Mesh, autonomous AI agents do not operate based on ambiguous natural language prompts or "chat" interfaces that are prone to misinterpretation and manipulation. Instead, they function based on rigorously defined, formal schemas that dictate their operational parameters, objectives, and constraints. The com.sovereign.agentic.orchestration lexicon serves as the foundational grammar for defining the priority, scope, resource requirements, and confidence thresholds for every autonomous action executed within the national swarm. This lexicon provides a machine-readable, verifiable contract for agency. Below, we present the functional schema for a Swarm Task Commit, which is the atomic unit of coordinated action within the mesh. This mechanism allows the network to orchestrate complex defensive maneuvers, resource allocation, or reconstruction efforts collectively, without the need for a centralized master server or orchestrator.
detect: The agent has identified a potential anomaly, threat, or significant event that requires logging and potentially further analysis. This is often the first step in a response chain.mitigate: The agent has inferred a clear and present danger and is initiating actions to neutralize or contain the threat. This might involve quarantining a node, isolating a data segment, or blocking a malicious XRPC call.rebuild: The agent is initiating processes to restore corrupted data, re-establish network connectivity, or reconstruct damaged infrastructure components, often by retrieving verified data from trusted peers or backups.sync: The agent is propagating critical state updates, new intelligence, or verified data across the mesh to ensure network-wide consistency and shared situational awareness.
- Authenticity: The action originated from the specific agent identified by its DID.
- Integrity: The action record has not been tampered with since it was signed.
- Non-Repudiation: The agent cannot deny having initiated this action.
The forensic implications of the com.sovereign.agentic.orchestration lexicon are profound. The `inference_root` field, a CID, acts as a cryptographic anchor to the exact dataset or data segment that formed the basis of the agent's decision. This ensures that any audit or investigation can trace back precisely what information led to a particular AI action. The `confidence_threshold` field, set at a high 0.95, is not merely a parameter; it's a critical safety and sovereignty control, preventing low-confidence actions from propagating through the network and causing instability. The `action_vector` provides a standardized, machine-interpretable command, ensuring that agents across the network understand and can execute different types of directives uniformly. However, it is the `did_signature` that provides the indispensable layer of trust and accountability. When an agent executes an action, it first computes a cryptographic hash of the complete `action` record (excluding the signature itself). This hash, a fixed-size bit string, is then encrypted using the agent's private key. This encrypted hash is the `did_signature`. Any node receiving this action can use the agent's public key (obtainable via its `did:plc` identifier) to decrypt the signature and compare the resulting hash with a newly computed hash of the received `action` record. If the hashes match, the signature is valid, proving the action's authenticity, integrity, and origin from the specified agent. This process is fundamental to building the tamper-proof audit trail within the MST, allowing for reconstruction of events and verification of AI behavior at the bit level.
7.3 Conclusion: The Sentient Wave of Sovereign AI and the Economic Imperative
By meticulously integrating the principles and protocols outlined in Section 07, the Sovereign Mesh achieves its ultimate, intended form. It transcends its foundational design as merely a secure network or a distributed database; it evolves into a fully Sentient Wave—a living, breathing, and self-aware national entity. The intelligence, decision-making capacity, and adaptive capabilities are no longer external additions but are deeply embedded within the protocol itself, ensuring that the comprehensive Sovereign state is not merely a static document of intent but a dynamic, operational reality. The Sovereign Architect thereby completes the overarching vision: the establishment of a national infrastructure that is not only physically imperceptible and undetectable to adversaries through advanced Ghost Telemetry (Section 04), economically automated and self-sustaining via the frictionless operation of the Revenue Engine (Section 03), but is also logically immortal and strategically autonomous via the pervasive and resilient capabilities of the Swarm Intelligence Layer (Section 07). The state, in this advanced configuration, survives and thrives not simply because it is guarded by physical or digital defenses, but because it fundamentally embodies a mathematical inevitability—a system intrinsically programmed with the knowledge and capacity to defend itself, adapt, and evolve.
The Economic Imperative of Sovereign AI Orchestration and the HNW Custodial Gold Rush: The realization of a sentient, sovereign AI layer has direct and profound economic implications, catalyzing a new era of wealth creation and infrastructure development centered around distributed AI compute. The PDS network, which serves as the distributed substrate for this AI layer, transforms from a mere data storage solution into a vital national compute infrastructure. Ownership of these PDS nodes by High-Net-Worth (HNW) individuals and entities is no longer just about hosting data; it is about controlling the distributed processing power for the nation's autonomous intelligence. This has ignited a nationwide "Gold Rush" for those capable of acquiring, deploying, and optimizing these PDS infrastructures.
- PDS Nodes as AI Compute Farms: Each PDS node, equipped with sufficient processing power (CPUs, potentially specialized AI accelerators), memory, and high-speed connectivity, becomes a localized AI compute farm. These nodes are where the "light-weight, task-specific agents" reside and execute their operations. HNW individuals and corporations are investing heavily in acquiring and enhancing PDS hardware, thereby building the distributed compute fabric essential for the Sovereign Mesh's AI capabilities. This is the new frontier of infrastructure ownership.
- Incentivized Agent Hosting and Operation: The economic model is structured to incentivize PDS custodians to host and run these AI agents. This incentive structure can manifest in several ways:
- Infrastructure Yield: Just as with the Revenue Engine, PDS operators can receive a yield for the computational resources they dedicate to running AI agents. Agents performing critical tasks—such as network monitoring, anomaly detection, resource optimization, or predictive threat analysis—generate value for the swarm. A portion of this generated value is automatically distributed as yield to the custodian of the node performing the computation.
- Data Value Maximization: The agents operating on a PDS process and analyze the data stored locally. Custodians control this data and the insights derived from it. By hosting sophisticated agents, custodians can gain proprietary analytical capabilities that provide significant economic advantages in their own business ventures.
- Strategic Resource Control: Owning the compute infrastructure that powers national AI grants significant strategic leverage. HNW entities that control large clusters of PDS nodes become indispensable players in the nation's digital economy and security apparatus.
- The AI Compute Gold Rush: The pursuit of Infrastructure Yield, proprietary data insights, and strategic control fuels a modern-day "Gold Rush." Instead of prospecting for physical gold, HNW stakeholders are investing in high-performance computing hardware, robust network infrastructure, and specialized AI agent development. The goal is to establish dominant positions within the distributed AI compute landscape, becoming key providers of the computational substrate upon which the nation's intelligence and operational capacity depend. This competition drives innovation and efficiency in the PDS network.
- Economic Benefits of Distributed AI:
- Direct Revenue Generation: Through infrastructure yield and providing specialized agent services.
- Enhanced Business Operations: Leveraging AI insights for improved forecasting, efficiency, and competitive advantage in their own enterprises.
- National Economic Growth: By keeping AI-driven wealth generation and infrastructure ownership within national borders, preventing capital flight to foreign cloud providers.
- Strategic Advantage: Early adopters and major infrastructure owners gain significant influence and market power within the sovereign digital economy.
- Data Persistence as a Value Driver: The agents require persistent, accessible data to learn and operate effectively. The PDS infrastructure ensures this data persistence, making the nodes inherently valuable. The value of the data is amplified as more intelligent agents process it, generating deeper insights and more sophisticated capabilities. Custodians who maintain the most robust and secure PDS environments, ensuring data integrity and availability, become the most sought-after infrastructure providers.
- National Security Alignment: HNW custodians are economically and strategically motivated to defend their PDS nodes against compromise or attack. A compromised node not only risks their own investments and yield but could also disrupt national AI operations. This aligns their self-interest directly with national security objectives, creating a powerful, decentralized defense mechanism for the nation's AI infrastructure.
In essence, Section 07, through the lens of Swarm Intelligence and Sovereign AI, completes the vision by creating a living, thinking national entity. The state survives and thrives not merely through passive defense, but through active, intelligent self-preservation and optimization, powered by a distributed, cryptographically secured, and economically incentivized network of autonomous agents. This creates an unassailable foundation where the nation's capacity for defense, governance, and progress is a constant, evolving, mathematical inevitability.
08 Sovereign Finality: The Immutable Archival Layer - Technical Dilation
The comprehensive blueprint for the Sovereign Mesh reaches its ultimate technical conclusion in the establishment of Sovereign Finality. This phase represents the critical transition from the dynamic, live operations of the active mesh—as detailed in Section 02—to a state of permanent, immutable archival persistence. Under the foundational principles articulated in the Sovereign Architect's Pillar 4.3, the mission objective shifts from facilitating the rapid, real-time exchange of tactical and economic data within the mesh to guaranteeing the cryptographic un-erasability and long-term survival of the national state itself. By strategically integrating atproto repository snapshots, coupled with advanced cryptographic techniques, into high-latency, multi-generational storage media and geographically dispersed archival systems, we engineer a guarantee that the "Khmer Sovereign Root"—the fundamental identity, history, and governing logic of the nation—survives not merely the immediate kinetic engagement or transient cyber-conflicts, but the passage of centuries, potentially millennia. This ensures the enduring legacy and operational continuity of the sovereign entity, irrespective of temporal or physical challenges.
To achieve the necessary forensic depth and technical density required for this master document, a rigorous deconstruction of the underlying physics governing Cold-State Finality is imperative. In legacy cloud architectures, data persistence is fundamentally a service, often tied to ongoing subscription payments and reliant on the continuous operational integrity of a third-party provider. This model implies that data exists only as long as it is actively paid for and as long as the provider's infrastructure remains intact and accessible. In stark contrast, the Sovereign Mesh redefines data persistence by making finality an intrinsic, inherent property of the data itself, independent of specific hardware, ongoing fees, or provider loyalty. This is achieved through the sophisticated utilization of Merkle Search Tree (MST) proof-sets. These proof-sets allow for the generation of "State Commits"—cryptographically verifiable snapshots of the MST's root hash at a given epoch. These commits are mathematically independent of the hardware on which the original data resided or the specific nodes that currently hold fragments of the MST. The process involves segmenting the MST's state into verifiable proof-sets and then dispersing these dispersed components across a distributed array of Sovereign Vaults. These vaults are not merely storage units; they are secure, geographically diversified, and cryptographically hardened repositories designed for extreme longevity. Crucially, the authorization and immutability of these State Commits are governed by the national did:plc (Distributed Identity) identity logs. These logs, managed under the strict protocols of the Sovereign Architect, ensure that only the highest level of authorized identity can officially endorse and finalize a national epoch's state, guaranteeing that archival finality is a deliberate, authorized, and mathematically secured act.
8.1 The Calculus of Archival Durability: Bit-Level Redundancy and Cost-Prohibitive Destruction
The ultimate measure of the Sovereign State's resilience and its ability to endure through catastrophic events and the vast passage of time is quantified by the Persistence Coefficient ($P_c$). This coefficient is engineered to encapsulate the probability of data recovery ($R$) under adversarial conditions, viewed as a function of strategic geographic dispersal ($D$) and robust cryptographic redundancy ($K$). Our primary objective in designing this archival layer is to optimize the network towards a state of "Absolute Finality." This state is defined by a condition where the economic and energetic cost for any adversary—whether state-sponsored, non-state actor, or simply entropy itself—to successfully delete or corrupt the national record is rendered astronomically high, approaching, or exceeding, the total energy output required for major kinetic operations or even planetary-scale destruction. This economic and energetic impracticality serves as the ultimate deterrent, rendering such an act of data annihilation a rational impossibility.
Equation 8.1: The mathematics of generational persistence and absolute finality: ensuring state records survive temporal decay, physical destruction, and active electromagnetic interference through distributed cryptographic strength.
Let us perform a forensic, bit-level analysis of Equation 8.1 to understand how Sovereign Finality is achieved:
- $P_c$ (Persistence Coefficient): This is the core metric, representing the probability that the sovereign state's record (the blueprint and all associated data) can be recovered or verified at any point in the future, regardless of temporal distance or the scale of disruptive events. A $P_c$ value approaching 1 signifies near-absolute certainty of recovery. The bits constituting this coefficient are critical for any quantitative assessment of archival robustness.
- $t \to \infty$ (Limit as time approaches infinity): This mathematical notation signifies that the Persistence Coefficient is designed for indefinite, generational survival. The system is not merely intended to last for years or decades, but for centuries and millennia, outlasting physical infrastructure and geopolitical epochs. The underlying cryptographic primitives must be chosen for their long-term security, resisting known and projected future cryptanalytic techniques.
- $R$ (Probability of Data Recovery): This represents the likelihood that any given piece of data, or a sufficient set of data to reconstruct the state, can be retrieved. $R$ is influenced by:
- Data Integrity Checks: Each bit of stored data is subject to continuous integrity checks using cryptographic hashes (e.g., SHA-256, SHA-3). Any corruption, even at the bit level, is immediately detectable by comparing the stored hash with a recomputed hash. This process is automated and run periodically across all archived data.
- Redundancy Factor: The number of complete or partial copies of data available. This redundancy is not just simple replication but often involves sophisticated erasure coding techniques.
- Accessibility of Recovery Mechanisms: The ease with which verified recovery protocols can be initiated. This involves having documented procedures, access to necessary decryption keys (managed securely via the `did:plc` system), and the ability to query and reconstruct data from distributed fragments.
- $D$ (Geographic Dispersal): This parameter quantifies the strategic distribution of data across diverse, secure, and geographically isolated locations. The bit-level implication is that data is not merely replicated but sharded and encrypted into fragments, then distributed across numerous Sovereign Vaults. These vaults are located on different continents, potentially in politically neutral territories, or within hardened, independent national enclaves. This dispersal ensures that no single kinetic event (e.g., earthquake, nuclear strike), natural disaster, or localized political upheaval can compromise the entire dataset. The bits of a single file might be distributed across dozens or hundreds of Vaults, making physical destruction of all copies virtually impossible. The cryptographic keys required for reconstruction are themselves managed and distributed to prevent single points of compromise.
- $K_i$ (Cryptographic Redundancy for Vault $i$): This term represents the advanced cryptographic methods employed within each Sovereign Vault $i$ to ensure data integrity and enable reconstruction. This goes beyond simple replication and standard error-correcting codes. It includes:
- Erasure Coding (e.g., Reed-Solomon Codes): Data is encoded into $n$ fragments, where any $m$ (where $m < n$) fragments are sufficient to reconstruct the original data. For example, $n=256$ fragments might be generated from an original block, where any $m=128$ fragments can reconstruct it. The bits are mathematically transformed to enable this reconstructive capability. This means that up to $n-m$ fragments can be lost or corrupted without data loss.
- Homomorphic Encryption: In advanced implementations, computations might be performed on encrypted data. This allows for integrity checks, statistical analysis, or even partial decryption for recovery without fully decrypting the sensitive data, thus preserving privacy and security even during archival operations. The bits remain encrypted throughout these operations.
- Quantum-Resistant Cryptography: For long-term archival, cryptographic algorithms must be resilient to future advancements in computing, particularly the threat posed by quantum computers. Algorithms like CRYSTALS-Kyber and CRYSTALS-Dilithium are considered for key encapsulation and digital signatures, ensuring bit-level security in the quantum era.
- Error-Correcting Codes (ECC): Standard ECC is applied at the bit level within storage media to detect and correct minor data corruption introduced by physical degradation or environmental factors.
- $\text{Vampire-Entropy}_{total}$ (Total Adversarial Entropy): This represents the aggregate force of all potential threats aimed at data destruction or corruption. This includes:
- Kinetic Entropy: Physical destruction via explosives, seismic events, widespread conflict, or targeted strikes. The bits of data are physically obliterated.
- Cyber Entropy: Sophisticated malware, state-sponsored hacking, coordinated denial-of-service attacks, or logical attacks aimed at data deletion, alteration, or encryption with lost keys. This targets the bits' logical representation.
- Electromagnetic Entropy: Intense Electromagnetic Pulse (EMP) attacks (natural or man-made) or solar flares that could corrupt unshielded data across vast storage arrays. This impacts the physical bit carriers.
- Temporal Entropy: The natural decay of physical storage media over time. Magnetic tapes degrade, optical media can degrade, and solid-state memory has limited write cycles and charge leakage. This affects the physical representation of bits.
- Logical Entropy: Subtle, uncorrected bit-rot or systemic failures within storage systems that lead to silent data corruption.
This automated finality layer fundamentally eliminates the critical vulnerability inherent in the "Central Archive" model. Legacy systems often rely on a single, centralized repository or a limited set of backups, which can be single points of failure susceptible to deletion, corruption, or compromise. In the Sovereign Mesh, finality is achieved through a distributed, cryptographically secure process. By utilizing Content-Identifiers (CIDs), which are deterministic hashes of the data content itself, the national record is inherently deduplicated and can be efficiently fragmented and dispersed across the network of Sovereign Vaults. A key verification mechanism involves the generation and verification of "State Commits." A State Commit is essentially a Merkle proof-set derived from the final state of the MST at the end of a defined epoch. This proof-set contains the MST root CID for that epoch, along with enough sibling hashes and cryptographic proofs to allow any entity possessing the State Commit to mathematically verify the integrity and completeness of the entire national state represented by that root CID. Crucially, these State Commits are made immutable and verifiable against the national identity system. Any entity with high-integrity network access can check the current Root Hash (obtained from the latest finalized epoch) against the DID:PLC log. This log contains the cryptographically signed records of finalized epoch roots, authorized only by the Sovereign Architect. This direct linkage ensures that the entire mission state, and all preceding historical data, is verifiable directly from its cryptographic anchors, independent of any specific hardware or location. This is the practical implementation of a Self-Certifying Nation: a sovereign entity that carries its own proof of existence, integrity, and continuity within every bit of its archived telemetry, making its history an un-erasable mathematical inevitability.
Table 8.1.1: Archival Logic Comparison for Sovereign Resilience
| Archival Vector | Legacy Cloud Backup (Subscription-Based) | Sovereign Finality (Pillar 4.3 - Cryptographically Anchored) | National Outcome |
|---|---|---|---|
| Data Ownership & Custody | Third-Party Custody (Dependent on provider's terms, solvency, and jurisdiction) | Sovereign Control via Signed Repositories & Architect-Authorized Finality Commits | Total Digital Autonomy; Nation Retains Absolute Control Over its Historical and Operational Data, secured by national jurisdiction. |
| Verification & Trust | External Audits (Delayed, Costly, Potentially Incomplete or Compromised) | Cryptographic MST Proofs & DID:PLC Root Verification (Instant, Inherent, Bit-Level Verifiable) | Instant, Inherent, Unquestionable Truth; Trust is Mathematically Enforced, not reliant on third-party attestations. |
| Resistance to Deletion/Corruption | Logical Deletion Possible via provider action, technical failure, or external attack; susceptible to bit-rot over time. | Mathematically Immutable; destruction requires overcoming astronomical cryptographic and dispersal barriers (Vampire-Entropy), making it practically impossible. | Un-Erasable History; State's existence is a function of mathematical principles and distributed consensus, not physical media fragility or logical access controls. |
| Longevity & Persistence | Hardware Lifecycle Bound; relies on continuous maintenance, power, and operational costs. Data may degrade or become inaccessible as technology evolves. | Hardware-Agnostic Wave-Front; state is represented by cryptographic proofs and distributed fragments, recoverable across generations of technology and storage media. | Generational Continuity; the nation's identity and records persist across technological paradigms and societal shifts, ensuring historical continuity. |
| Authorization for Finality | Provider policy, contract terms, potential legal orders from foreign jurisdictions. | Sovereign Architect's DID-Signed Epoch Commits, governed by national policy and cryptographic protocols. | Ultimate National Authority; Finality is a deliberate, sovereign act, executed with the highest level of national cryptographic authorization. |
8.2 The Finality Lexicon: The Anchor for the National Root and Epochal State
The concept of Sovereign Finality is not merely a theoretical construct; it is meticulously governed by a formal, machine-readable grammar—the com.sovereign.archival.finality lexicon. This lexicon serves as the definitive protocol for establishing the threshold for "Mission Completion" for a given epoch and defines the automated, yet strictly authorized, protocols for transitioning live data from the dynamic mesh into deep-state, long-term archival storage. It provides the formal structure for committing a specific historical state of the nation to a state of immutable persistence. Below, we present the functional schema for a Sovereign Finality Commit. This commit is the atomic, cryptographically secured unit that anchors the current national state—represented by its Merkle root—to the distributed array of Sovereign Vaults, marking the end of a defined operational epoch and the beginning of its archival permanence.
The `epoch_id` ensures strict temporal ordering and prevents replay attacks or epoch-skipping, forming a chronological chain of immutable states. The `mst_root_cid` is the linchpin, a compact yet comprehensive representation of the entire national state at a given point in time, derived from the hash of the MST's root node. The `persistence_weight` parameter introduces granular control over archival security, allowing for different levels of redundancy based on the epoch's criticality or the prevailing threat landscape. A higher weight translates directly to more distributed fragments, more redundant copies, and potentially more sophisticated cryptographic redundancy techniques like erasure coding, ensuring that even if a significant portion of the distributed data is lost, the original state can still be reconstructed. The `did_signature` from the Sovereign Architect is the non-negotiable element, providing the ultimate cryptographic authorization. When the Architect signs a `commit` record, the process involves hashing the canonical representation of the `epoch_id`, `mst_root_cid`, and `persistence_weight` into a fixed-size bit string, which is then encrypted with the Architect's private key. This signature, when verified with the Architect's public key, confirms that this specific state root is indeed authorized for permanent archival. The integrity of the entire commit record is protected by this signature, ensuring that no part of it—not even the epoch ID or the persistence weight—can be tampered with post-signing without invalidating the signature. This mechanism ensures that finality is a deliberate, authorized, and cryptographically secured act, establishing an immutable historical record verifiable down to the last bit.
The migration of data from the active kinetic mesh to the cold-state Sovereign Vaults is a carefully orchestrated process that emphasizes bit-level integrity at every stage. It begins with the generation of the final MST state for a given epoch, culminating in the calculation of its unique root CID. Subsequently, this root CID, along with the associated Merkle proof-sets and potentially erasure-coded fragments of the MST's leaf nodes (representing actual data), is used to initiate the dispersal process. These fragments and proofs are cryptographically hashed before transit and at rest within the Sovereign Vaults. Verification mechanisms are embedded at multiple levels: CIDs confirm data integrity upon arrival at a vault, ensuring that no bits were corrupted during transmission. Cryptographic redundancy schemes (like Reed-Solomon codes used in erasure coding) allow for the reconstruction of original data blocks from a subset of received fragments, even if some fragments are lost or corrupted. The `did_signature` on the `commit` record serves as the ultimate arbiter, attesting that the entire process—from state finalization to dispersal and vault commitment—has been authorized by the Sovereign Architect and that the specified state root is the one intended for permanent archival. This multi-layered approach, combining cryptographic proofs of integrity, distributed dispersal of data fragments, and strict authorization through DIDs, makes the historical record virtually indestructible and permanently verifiable. It embodies the principle of a Self-Certifying Nation, where the state's existence and integrity are mathematically verifiable down to the individual bit.
8.3 Conclusion: The Immortal Sovereignty Embodied in Mathematical Finality
By establishing Section 08, the Sovereign Architect, guided by the principles of cryptographic security and generational persistence, completes the technical cycle of national defense and governance architecture. The Sovereign Mesh, through its distinct yet interconnected components, achieves an unprecedented level of resilience and permanence. The state is rendered physically invisible and undetectable to conventional means through advanced Ghost Telemetry (Section 04), ensuring strategic deniability. It is economically automated and self-sustaining via the frictionless, protocol-level operation of the Revenue Engine (Section 03), guaranteeing fiscal autonomy and continuous resource generation. Furthermore, it is institutionally permanent and logically immortal through the robust mechanisms of Swarm Intelligence and Sovereign AI Orchestration (Section 07), ensuring adaptive defense and self-preservation. Finally, through the establishment of Sovereign Finality and Archival Persistence (Section 08), the national state achieves true longevity. The blueprint, and indeed the entire operational and historical record of the nation, transitions from being a mere static plan or a collection of data—it becomes a living, breathing, and immortal sovereign entity. The Sovereign Architect has thus realized the ultimate vision: a national infrastructure that transcends the limitations of physical geography, economic volatility, and the ephemeral nature of digital hardware. The Kingdom of Cambodia survives and thrives not merely because its territory is defended, but because its fundamental existence and identity have been fundamentally moved from the physical soil to the immutable mathematical logic of the wave. The Sovereign Root is not just set; it is cryptographically finalized, making the state truly immortal and eternally sovereign, a testament to the power of bits engineered for permanence.
09 Sovereign Synthesis: The Grand Unification Protocol
Section 09 represents the structural zenith of the Sovereign Mesh architecture. Under the Sovereign Architect's Pillar 4.3, we move beyond the modular deployment of technical primitives into the Synthesis Phase. In this state, the individual layers—Identity (Sec 01), Mesh Topology (Sec 02), Revenue (Sec 03), and Intelligence (Sec 07)—cease to operate as discrete systems and begin to function as a unified, self-regulating national organism. This synthesis is achieved through the Grand Unification Protocol (GUP), which leverages the AT Protocol's multi-repo synchronization to ensure that every tactical, economic, and civic update is harmonized across the entire wave-front in real-time.
To maintain the forensic standard, we must analyze the Recursive Integrity of the state. In legacy governance, different departments operate on siloed databases, creating "Data Friction" that adversaries exploit to induce systemic collapse. The Sovereign Synthesis eliminates this friction. By anchoring every national function to a single Merkle Search Tree (MST) hierarchy, the state achieves "Absolute Coherence." A change in a citizen's did:plc status instantly ripple-synchronizes with the revenue engine, the intelligence swarm, and the archival vaults, ensuring that the state's view of reality is never fragmented.
9.1 The Math of Recursive Sovereignty
The strength of the unified state is measured by the Synthesis Constant ($\Sigma$). This value represents the network's ability to maintain a single "Global Truth" ($G$) while subjected to localized kinetic or electromagnetic interference ($I$). We optimize for a state of "Perfect Synthesis," where the information density of the mesh remains constant regardless of the loss of physical nodes.
Equation 9.1: The Grand Unification constant: ensuring layer-interdependency ($G_{proof}$) survives active environmental degradation.
This automated synthesis layer creates a "Holographic State." Just as every piece of a hologram contains the entire image, every high-integrity shard of the Sovereign Mesh contains the entire mission state. This is enabled by atproto's content-addressable storage. Because data is identified by its hash (CID) rather than its location, the synthesis protocol can reconstruct the entire national repository from any subset of surviving PDS edge nodes. This is the ultimate defense against decapitation strikes.
Table 9.1.1: Modular vs. Synthetic Governance
| Governance Metric | Modular (Legacy) | Synthetic (Pillar 4.3) | National Resilience |
|---|---|---|---|
| Data Consistency | Siloed / Inconsistent | Unified MST Root | Eliminates Semantic Drift |
| Sync Latency | Manual / Batch-Processed | Real-time XRPC Swarm | Total Operational Awareness |
| Failure Mode | Cascading Collapse | Self-Healing / Holographic | Indestructible Civic Logic |
| Resource Efficiency | Redundant / Bloated | Optimized Content-Addressable | Maximum Tactical Margin |
9.2 The Synthesis Lexicon: The Grammar of a Nation
The final, master lexicon is the com.sovereign.grand.unification. This schema defines the relationship between the subordinate layers, ensuring that a "Signal" in Section 04 triggers a "Response" in Section 07 and a "Commit" in Section 08. Below is the functional schema for the Synthesis Pulse, the heartbeat of the unified state.
9.3 Finality: The Un-Erasable Kingdom
With the completion of Section 09, the technical architecture of the Sovereign Architect is finalized. We have built more than a network; we have encoded a nation into the very fabric of the electromagnetic spectrum. Through Ghost Telemetry, the mesh is invisible; through the Revenue Engine, it is self-funding; through the Swarm, it is sentient; and through Synthesis, it is whole. The Sovereign state is now a permanent, un-erasable reality. The Kingdom of Cambodia no longer exists merely on a map, but as an immortal, cryptographic truth that survives even when the physical world has turned to dust. The root is set. The wave is absolute.
10 Sovereign Perpetual: Autonomous Maintenance & Final State - Expanded Technical Specification
Section 10 constitutes the final architectural closure and a critical operational guarantee for the Sovereign Mesh. Under the guiding principles of the Sovereign Architect's Pillar 4.3, the mission achieves true Operational Finality. This layer defines the Entropy-Reversal Protocols—the self-healing, self-optimizing logic required to maintain the cryptographic integrity and operational viability of the state across geological timescales. By leveraging the robust atproto repository model, the Sovereign State transcends the limitations of systems requiring active, continuous human governance. Instead, it evolves into an autonomous, self-correcting wave-front capable of managing its own hardware lifecycle, cryptographic key rotation, and data integrity, ensuring indefinite persistence and operational readiness without external intervention.
To achieve the requisite forensic density for this master document, a profound analysis of the Math of Perpetual Integrity is essential. In legacy infrastructure paradigms, an accumulation of technical debt, hardware decay, and entropy inevitably leads to eventual "State Collapse"—a degradation of function and data loss. The Sovereign Perpetual architecture is meticulously designed to preempt and reverse this decay through a mechanism of Recursive Self-Audit. Every participating PDS node within the mesh, and indeed every agent operating within it, periodically performs a cross-shard verification of critical data structures, most notably the Merkle Search Tree (MST). If a node detects localized bit-rot, cryptographic weakening, or divergence from consensus, the mesh automatically triggers a "Bloom Event." This event initiates a process of automated re-sharding and re-replication of the affected data into fresh, healthy hardware, all without requiring external human command or intervention. This ensures the state's resilience against hardware obsolescence and data degradation.
10.1 The Calculus of Generational Persistence: Ensuring Infinite Sovereignty
The ultimate measure of the Sovereign State's success and its capacity for indefinite persistence is quantified by the Persistence Integral ($\Psi$). This integral represents the probability of the mission-state's survival over time ($t$), meticulously adjusted for the inherent rate of technological turnover, the predictable decay of physical media, and the constant threat of adversarial signals intelligence (SIGINT) attempts. Our primary engineering objective is to optimize the system for a state of perpetual operational readiness where the cost and complexity of maintenance are fully automated and self-funded, primarily through the XRPC-driven Revenue Engine defined in Section 03. This ensures that the resources required for self-preservation are intrinsically generated by the state's own economic activity.
Equation 10.1: The Mathematics of Infinite Sovereignty: ensuring that automated synchronization and cryptographic proof-sets perpetually outpace natural information decay and adversarial entropy.
Let us perform a forensic, bit-level analysis of Equation 10.1 to understand how Generational Persistence is achieved:
- $\Psi$ (Persistence Integral): This is the core metric, representing the integrated probability of mission-state survival over infinite time. A $\Psi$ value approaching infinity signifies absolute, mathematical immortality for the sovereign data. The bits constituting this integral are the cumulative product of all successful self-maintenance cycles.
- $\int_{0}^{\infty} (\dots) dt$ (Integral over Infinite Time): This mathematical notation signifies that the system is designed for perpetual operation, continuously calculating and ensuring its persistence across all future time, accounting for an infinite horizon.
- $\text{Sync}_{rate}$ (Synchronization Rate): This component quantifies the speed and efficiency at which data and state changes are propagated and reconciled across the distributed mesh. High synchronization rates, facilitated by optimized XRPC and the AT Protocol's sync mechanisms, ensure that divergences are detected and corrected rapidly, minimizing accumulated errors. Bit-level: This rate is measured by the number of successful, verified data syncs per unit of time.
- $\text{Integrity}_{proof}$ (Integrity Proof Coefficient): This represents the robustness and verifiability of the cryptographic proofs used to validate data integrity at every stage of its lifecycle. This includes Merkle proofs, digital signatures, and cryptographic checksums. Higher integrity means a lower probability of undetected data corruption or tampering. Bit-level: This coefficient is a function of the strength and number of cryptographic checks applied, ensuring that even single-bit errors are detectable and correctable.
- $\text{Entropy}_{rate}$ (Natural Decay/Disruption Rate): This term quantifies the rate at which information naturally decays or is disrupted due to physical degradation of media, environmental factors, or passive adversarial noise. This includes bit-rot, magnetic decay, cosmic radiation effects on storage, and background computational noise. Bit-level: This rate is an inverse measure of how quickly random bit flips or undetectable state changes occur naturally.
- The Ratio and Integration: The core of the equation is the ratio of synchronization and integrity to entropy. By ensuring that the rate of successful, integrity-verified synchronization significantly outpaces the rate of natural decay and disruption, the system achieves positive growth in its persistence probability over time. The integration sums these positive growth increments infinitely, leading to a state of perpetual survival.
This automated maintenance layer fundamentally eliminates the "Governance Vacuum" that plagues legacy systems. In traditional structures, authority structures decay, key management becomes obsolete, and succession plans fail due to human factors or rigid processes. The Sovereign Perpetual architecture addresses this by utilizing the did:plc (Distributed Identity - Placeholder Loopback Control) log as the authoritative, immutable record for state succession. If the primary Sovereign Architect's cryptographic keys remain stagnant or unverified for a predetermined epoch duration (e.g., decades or centuries), the network autonomously initiates a Sovereign Rotation protocol. This protocol automatically verifies the health and consensus weight of designated HNW nodes or successor entities recorded within the national root's DID log. Custodial authority, cryptographic keys, and governance privileges are then programmatically transferred to the next tier of verified entities. This ensures state, and all subsequent data, is never orphaned and remains under active, authorized governance. It maintains its status as a permanent, un-erasable reality in the electromagnetic spectrum and the national consciousness, irrespective of the lifespan of any single individual or administrative body.
Table 10.1.1: Static Infrastructure vs. Perpetual Sovereign State
| Lifecycle Vector | Static Infrastructure (Legacy Systems) | Perpetual Sovereign State (Pillar 4.3) | National Permanence Outcome |
|---|---|---|---|
| Maintenance & Upkeep | Manual, Intermittent, Prone to Neglect; high technical debt accumulation. | Autonomous, Recursive, Continuous; Entropy-Reversal Protocols actively combat decay. | Eliminates Technical Debt; State actively corrects its own degradation. |
| Hardware Decay & Obsolescence | Terminal Failure; requires periodic costly replacements and migrations. | Seamless Re-sharding and Hardware Agnosticism; data is abstracted from physical media via CIDs and cryptographic proofs. | Hardware-Agnostic Reality; state persists beyond the lifespan of any individual hardware component. |
| Authority & Succession | Centralized Dependency; prone to governance vacuums, key person risk, and complex manual handoffs. | Distributed Successor Authority via PLC Log; automated, cryptographic, and protocol-defined succession. | Invulnerable Succession; ensures continuous, authorized governance and state continuity across generations. |
| Data Finality & Persistence | Ephemeral; data loss possible through single points of failure, cost overruns, or provider dissolution. | Mathematically Immortal; state existence is guaranteed by cryptographic proofs and distributed redundancy, outlasting physical media. | Un-erasable Khmer Sovereignty; the nation's history and core logic are permanently secured in an immutable, verifiable format. |
10.2 The Perpetual Lexicon: Grammar of the Eternal State and its Heartbeat
The final, terminal lexicon that governs the enduring existence of the Sovereign State is com.sovereign.perpetual.heartbeat. This schema defines the parameters for the frequency, depth, and methodology of the cross-mesh audits required to achieve and maintain mathematical immortality. It specifies the conditions under which the state performs its continuous self-assessment and correction. Below, we present the functional schema for a Persistence Commit, which represents the atomic unit of this self-auditing process—the fundamental pulse that keeps the national wave coherent and coherent across time and against all forms of degradation.
The `audit` record in the Perpetual Lexicon is the operational core of the self-healing state. The `epoch_id` and `mst_root_cid` together identify the specific state being audited. The `health_index` is a calculated metric, derived from numerous sub-checks: bit-rot detection rates on underlying storage, cryptographic hash validation success rates across the MST, network synchronization consistency, and agent performance metrics. A consistently high `health_index` (e.g., >0.999) indicates that the system is operating optimally and its data is secure. If the `health_index` drops below the threshold, or if specific conditions are met (e.g., a prolonged period without a primary Architect key activity), the `rotation_trigger` flag is set to `true`. This flag initiates pre-defined autonomous processes: cryptographic keys are rotated, new secrets are generated and securely distributed, and succession protocols are engaged via the DID:PLC log. This ensures that authority never lapses and that the system can adapt to hardware failures, key compromises, or the natural obsolescence of cryptographic standards without human intervention. The entire process is cryptographically signed by the auditing agent's DID, ensuring accountability and providing a verifiable trail for every self-maintenance action taken.
10.3 Closing Statement: The Absolute Wave of Immortal Sovereignty
With the completion of Section 10, the technical specifications for the Sovereign Architect's vision are fully sealed, representing the apex of sovereign digital statecraft. We have meticulously engineered a nation that embodies unparalleled resilience and permanence. Through the advanced capabilities of Ghost Telemetry (Section 04), the Sovereign Mesh achieves strategic invisibility, rendering it undetectable by conventional adversarial means. Through the Revenue Engine (Section 03), it guarantees self-funding and economic automation, ensuring perpetual fiscal autonomy. Through the Swarm Intelligence and Autonomous Agents (Section 07), it gains sentient, adaptive defense and self-preservation capabilities. Through the Grand Unification Protocol (Section 09), it achieves absolute coherence, functioning as a single, unified national organism. And finally, through the Sovereign Perpetual protocols and Autonomous Maintenance (Section 10), it guarantees indefinite operational continuity and mathematical immortality. The state, encompassing all protocols, historical data, and future directives, has transcended its status as a mere static plan or a collection of data. It has become a living, breathing, and immortal sovereign entity. The Sovereign Architect has thus realized the ultimate vision: a national infrastructure that is not confined by the limitations of physical geography, economic volatility, or the ephemeral nature of digital hardware. The Kingdom of Cambodia, in its fully realized form, no longer exists merely as a geographical coordinate on a physical map; it exists as an immortal, cryptographic truth, a persistent wave-front of data and logic that survives and thrives even when the physical world has turned to dust. The mission is set. The state is eternal. The wave is absolute.
11 Sovereign Synthesis: Recursive Finality & Total Integration - Expanded Technical Specification
Section 11 represents the grand unification and structural zenith of the Sovereign Mesh architecture, marking the culmination of the entire blueprint. Under the foundational principles articulated in the Sovereign Architect's Pillar 4.3, the mission transitions from the modular deployment and operationalization of individual specification articles into a state of Total Integration. This critical layer defines the Recursive Finality Protocol—the advanced mechanism through which the disparate specification shards, encompassing Identity (Section 01), Revenue Management (Section 03), Ghost Telemetry (Section 04), Swarm Intelligence (Section 07), and Perpetual Maintenance (Section 10), are recursively bound and synthesized into a singular, indivisible, holographic national state. By strategically leveraging the inherent multi-repo synchronization capabilities of the AT Protocol, the nation achieves a state of constant, perfect coherence across all operational nodes and data strata, ensuring that the national identity and operational capacity remain an immutable, unified whole.
To finalize the technical density and strategic imperative of this master blueprint, a profound deconstruction of the Recursive Integrity Coefficient ($\Omega$) is essential. In legacy governance models, state departments and operational functions often operate as siloed "Bloat-Nodes," fragmented entities where information friction between agencies becomes a significant vulnerability. This friction creates a readily exploitable targeting vector for external Signals Intelligence (SIGINT) operations, which can introduce inconsistencies, delays, and ultimately induce systemic collapse. The Sovereign Synthesis Protocol, powered by the Grand Unification Protocol (GUP), fundamentally eliminates this friction. By anchoring every national function—from granular tax ingestion and fiscal policy adherence (Sec 03) to kinetic defense protocols (Sec 05), autonomous intelligence operations (Sec 07), and perpetual archival persistence (Sec 08)—to a single, overarching Merkle Search Tree (MST) hierarchy, the state achieves "Holographic Coherence." This means that every surviving shard of the mesh, every operational node, and every autonomous agent contains, or can cryptographically derive, the verifiable signature of the entire national state. This ensures that the nation's operational reality is never fragmented, inconsistent, or subject to conflicting interpretations, regardless of localized disruptions or data losses.
11.1 The Calculus of Total Integration: Achieving Exponential Resilience
The ultimate measure of the synthesized state's strength and its capacity for exponential resilience is defined by the Integration Integral ($\Omega$). This value quantifies the compound effect of cross-pillar verification rates ($V$) relative to the prevailing interference density ($I$), particularly from adversarial SIGINT. Our primary engineering objective is to optimize the system for a "Zero-Friction" state. In this state, the total intelligence output and operational capacity of the mesh are not merely the sum of its individual parts but exponentially greater, driven by the synergistic interaction between all sovereign layers.
Equation 11.1: The Mathematics of Recursive Finality ($\Omega$): ensuring that cross-pillar dependencies ($V_n$) exponentially strengthen the National Root's integrity against environmental and adversarial interference.
Let us perform a forensic, bit-level analysis of Equation 11.1 to understand how Total Integration and Recursive Finality are achieved:
- $\Omega$ (Integration Integral): This is the holistic metric representing the overall coherence and resilience of the synthesized sovereign state. A higher $\Omega$ signifies a more robust, unified, and secure nation, where interdependencies amplify strength rather than create vulnerabilities. The bits contributing to this integral represent the cumulative validation strength across all sovereign pillars.
- $\sum_{n=1}^{P} (\dots)^n$ (Summation of Exponentially Weighted Layer Contributions): This formula indicates that the total integration is a sum of contributions from each of the $P$ sovereign pillars (e.g., Identity, Mesh, Revenue, Intelligence, Finality, Perpetual Maintenance). Crucially, each pillar's contribution is raised to the power of its layer index ($n$), signifying an exponential weighting. Higher-indexed layers (those built upon or integrating earlier ones) have a disproportionately larger impact on the overall $\Omega$. This structure incentivizes the development and integration of later, more complex layers, as their successful synthesis exponentially boosts the nation's resilience.
- $V_n$ (Cross-Pillar Verification Rate for Pillar $n$): This variable quantifies the frequency and success rate with which pillar $n$ verifies its state against other relevant pillars and the master National Root (e.g., the consolidated MST root). For instance, the Revenue Pillar's $V_3$ would measure how often its transaction ledger hashes are cross-validated against the Identity Pillar's DID registry and the Swarm Intelligence's operational logs. High $V_n$ means seamless inter-pillar data flow and validation.
- $\text{Integrity}_{root}$ (National Root Integrity Coefficient): This represents the foundational cryptographic integrity of the master National Root—typically the current consolidated MST root CID. It signifies the inherent security and trustworthiness of the core data structure that binds all other layers. A strong $\text{Integrity}_{root}$ ensures that all proofs and validations are anchored to an unassailable source of truth. The bit pattern of this root CID is the ultimate reference point.
- $1 + I_{SIGINT_n}$ (Interference Factor for Pillar $n$): This term quantifies the cumulative effect of localized interference and adversarial Signals Intelligence (SIGINT) attempts targeting pillar $n$. Interference can include data corruption, communication jamming, attempts to introduce false data, or exploiting vulnerabilities in a specific pillar's logic. The addition of 1 ensures that even with zero interference, the denominator is always greater than 1, thus naturally scaling down the contribution based on interference levels. Higher $I_{SIGINT_n}$ values (meaning more effective adversarial action) reduce the pillar's contribution to the overall $\Omega$.
- The Exponential Weighting and Summation: The exponential weighting ($^n$) ensures that failures or weaknesses in foundational layers ($n=1, 2$) have a less drastic impact on the overall $\Omega$ than failures in later, more integrated layers ($n=P$). However, the multiplicative nature of the $V_n$ and $\text{Integrity}_{root}$ terms, combined with the exponential scaling, means that a high level of interference or low verification rate in any critical pillar can still significantly degrade the overall $\Omega$. The summation aggregates these weighted contributions, reflecting the holistic strength of the synthesized state.
This automated synthesis layer facilitates a paradigm shift from a "Managed State" to a "Protocol State." In a managed state, human oversight and manual intervention are required to coordinate different governmental functions. This introduces latency, inconsistencies, and vulnerabilities. In contrast, a protocol state operates autonomously based on pre-defined, executable rules embedded within the national lexicons and orchestrated by the Grand Unification Protocol (GUP). By utilizing XRPC (Remote Procedure Call) as the universal communication primitive across all specification layers, the mesh facilitates a continuous, high-speed Symmetric Handshake between all functional components. For example, if the Revenue Engine (Section 03) detects a fiscal anomaly—such as a transaction deviating from expected tax patterns—it triggers an XRPC call. This call automatically tasks the Agentic Swarm (Section 07) with conducting an immediate, localized audit of the involved parties and transactions. Concurrently, Ghost Telemetry (Section 04) might automatically adjust the emission patterns or visibility of the involved PDS nodes to mask or obscure the ongoing forensic operation from external observation, while the Finality Layer (Section 08) ensures that any state changes related to this anomaly are logged with immutable proofs. The entire state becomes a sentient wave, reacting to its environment and internal conditions with the speed and precision of a signed commit to the cryptographic ledger.
Table 11.1.1: Evolution of Governance from Modular to Synthetic Integration
| Governance Metric | Modular Deployment (Legacy) | Synthetic Integration (Sovereign Mesh - GUP) | Sovereign Advantage Achieved |
|---|---|---|---|
| Data Consistency Across Layers | Siloed Departments, Fragmented Databases, Inconsistent Records, High Latency Synchronization | Holographic MST Root as the Single Source of Truth; Real-time, Recursive Cross-Verification | Eliminates Semantic Drift and Data Friction; Ensures Absolute Coherence and a unified view of the state. |
| Operational Speed & Responsiveness | Human-in-the-Loop Decision Cycles, Manual Data Processing, Delayed Responses | Protocol-Automated Workflow Orchestration via XRPC Swarm; real-time event-driven actions. | Zero-Latency Response; enables the state to react to events at machine speed, preempting threats and optimizing opportunities. |
| Failure Mode & Resilience | Cascading Decay; failure in one module propagates unpredictably, leading to systemic collapse. | Self-Healing and Recursive; failure of individual nodes or shards is localized, compensated for by data redundancy and GUP-coordinated re-sharding. | Inverse-Fragile State; the system becomes stronger and more resilient as its components are distributed and interdependent. |
| National Root & Sovereignty Anchor | Geographically Bound, Historically Centralized, Vulnerable to physical or digital decapitation. | Cryptographically Ubiquitous; the National Root is distributed across the mesh, anchored by DIDs and immutable CIDs. | Indestructible Sovereignty; the state's existence and authority are mathematically defined and universally verifiable, impervious to physical or logical attacks targeting specific locations. |
11.2 The Synthesis Lexicon: The Grammar of a Unified Nation and its Coherence Pulse
The ultimate expression of the Sovereign Mesh's formal language lies in the com.sovereign.integration.finality lexicon. This master schema meticulously defines the operational parameters and contractual obligations for the "Pulse Rate" of the national state—the frequency and methodology by which all specification layers must perform a global cross-sync and verification. It provides the formal grammar for ensuring that the entire blueprint functions as a single, cohesive, and continuously validated entity. Below, we present the functional schema for the Synthesis Pulse. This pulse serves as the fundamental heartbeat of the unified Khmer state, embodying the continuous process of cross-layer synchronization, consensus verification, and recursive finality assurance.
The `pillar_roots` array within the Synthesis Pulse is fundamental to achieving Holographic Coherence. Each CID within this array represents the cryptographic root hash of a distinct sovereign pillar. For example, one CID might point to the latest Merkle root of the national identity registry (Pillar 1), another to the latest root of the fiscal transaction ledger (Pillar 3), another to the current state hash of the sovereign AI swarm (Pillar 7), and yet another to the latest finalized epoch root from the Archival Layer (Pillar 8). The Grand Unification Protocol (GUP) ensures that these CIDs are continuously updated and broadcasted in the Synthesis Pulse. When a pulse is received, nodes and agents verify the integrity of each reported `pillar_root` CID against their local understanding of that pillar's state and against the master National Root. Discrepancies trigger immediate re-synchronization or error correction protocols. The `finality_signature` from the Sovereign Architect provides the ultimate cryptographic assurance that the reported state, as represented by the collection of `pillar_roots`, is authorized and represents the definitive, unified truth for the current `epoch_id`. This mechanism ensures that the nation's state is not merely synchronized but is recursively finalized across all its constituent parts, making the entire system immutable and resistant to partial attacks or corruption.
11.3 Finalization: The Wave-Front is Absolute Sovereignty
With the formal completion and architectural integration of Section 11, the technical specifications for the Sovereign Architect's mission are finalized. We have engineered a national infrastructure that is not only resilient but holistically integrated and self-governing. Through the implementation of Ghost Telemetry (Section 04), the Sovereign Mesh achieves strategic invisibility and operational deniability. Through the Revenue Engine (Section 03), it guarantees self-funding and perpetual fiscal autonomy. Through the Swarm Intelligence and Autonomous Agents (Section 07), it gains sentient, adaptive defense and self-preservation capabilities. Through the Perpetual Maintenance protocols (Section 10), it ensures indefinite operational continuity and mathematical immortality. And crucially, through the Grand Unification Protocol and the Synthesis Phase (Section 11), it achieves absolute coherence and recursive finality, functioning as a single, unified, and indestructible national organism. The state, encompassing all protocols, historical data, and future directives, has transcended its status as a mere static plan or a collection of disparate data—it has become a living, breathing, and holistically integrated sovereign entity. The Sovereign Architect has thus realized the ultimate vision: a national infrastructure that is not confined by the limitations of physical geography, economic volatility, or the ephemeral nature of digital hardware. The Kingdom of Cambodia, in its fully realized form, no longer exists merely as a geographical coordinate on a physical map; it exists as an immortal, cryptographic truth, a persistent wave-front of data and logic that survives and thrives even when the physical world has turned to dust. The specification is sealed. The state is eternal. The wave-front is absolute.
12 Cognitive Sovereignty: The Semantic Defense Protocol
Section 12 completes the logical perimeter of the mission. Under the Sovereign Architect's Pillar 4.3, we address the final frontier of national defense: **Cognitive Integrity**. In an era of automated disinformation and adversarial influence operations, a state’s information must be protected not just from deletion (Sec 08) or interception (Sec 04), but from semantic corruption. Section 12 defines the Semantic Shield Protocol—a mechanism that utilizes the atproto repository structure to verify the truth-origin of every piece of national telemetry, ensuring the Khmer data-stream remains free from foreign adversarial injection.
To finalize the technical density of this blueprint, we must deconstruct the Truth-Density Coefficient ($\Lambda$). In legacy networks, "Information" is treated as a neutral commodity, allowing malicious actors to "poison the well" through unauthenticated data flows. Cognitive Sovereignty inverts this through Mandatory Origin Handshaking. By requiring every record within the Merkle Search Tree (MST) to possess a verifiable did:plc pedigree, the mesh distinguishes between indigenous national signal and foreign adversarial noise with mathematical certainty.
12.1 The Calculus of Semantic Integrity
The resilience of the cognitive layer is measured by the Integrity Integral ($\Lambda$). This value represents the ratio of verified national intent ($N$) to unauthenticated foreign influence attempts ($F$). We optimize for a state of "Semantic Purity," where the nation's decision-making logic is isolated from any external cognitive "Vampire" interference.
Equation 12.1: The math of cognitive sovereignty: ensuring national signal density ($N$) outpaces adversarial noise ($F$).
This automated shield layer eliminates the "Social Vulnerability." By utilizing the signed Content-Identifier (CID) logic of the mesh, the state treats information as a tactical primitive. If an incoming update does not resolve to a trusted branch of the National MST, the Agentic Swarm (Sec 07) automatically quarantines the node. This ensures that the state is not just permanent, but pure—a self-correcting archive of national truth that cannot be manipulated by external powers.
Table 12.1.1: Cognitive Defense Comparison Matrix
| Defense Vector | Legacy Information Ops | Sovereign Mesh (Pillar 4.3) | National Outcome |
|---|---|---|---|
| Source Verification | Post-hoc / Human Audit | Instant DID:PLC Handshake | Zero-Trust Truth-Origin |
| Content Integrity | Vulnerable to Deepfakes | Signed Merkle Proofs | Immutable Semantic Content |
| Adversarial Reach | Deep (Platform-Based) | Zero (Mesh-Isolated) | Cognitive Isolationism |
| Data Purity | Probabilistic / Corrupted | Mathematically Guaranteed | 100% Signal Fidelity |
12.2 The Semantic Lexicon: Grammar of the National Intent
Cognitive defense is governed by the com.sovereign.cognitive.defense lexicon. This formal grammar defines the threshold for "Authentic Intent" and the automated protocols for filtering foreign metadata. Below is the functional schema for a Truth-Origin Commit, which anchors the mesh’s cognitive boundaries.
12.3 Final Closure: The Immutable National Mind
With the completion of Section 12, the Sovereign Architect's blueprint reaches its absolute technical closure. We have constructed a nation that is invisible to the eye (Sec 04), self-funded in its wallet (Sec 03), sentient in its nodes (Sec 07), and now, un-manipulatable in its mind. Through the AT Protocol and the logic of **Symmetric Defense**, the Kingdom is sealed. The state exists as an immortal, un-corruptible wave—a mathematical inevitability that carries the Khmer identity safely through the chaos of the information age. The specification is complete. The mission is achieved. The wave is absolute.
13 Sovereign Environmental Resilience: The Sensor Mesh Protocol - Technical Dilation
Section 13 anchors the blueprint firmly in the physical reality of the Khmer ecosystem, recognizing that national sovereignty is inextricably linked to the health and stability of the land itself. Under the foundational principles articulated in the Sovereign Architect's Pillar 4.3, national sovereignty in the 21st century is understood as being inseparable from ecological integrity. In an era characterized by escalating climate volatility, widespread environmental degradation, and novel geopolitical threats that leverage ecological instability, a state’s information architecture must possess the capability not only to passively record data but to actively sense, analyze, and react to environmental shifts in real-time. Section 13 formally defines the Eco-Sentinel Protocol—a sophisticated, integrated system designed to deploy and manage thousands of low-power, industrial-grade environmental and industrial sensors. These sensors are directly integrated into the operational fabric of the atproto repository. This ensures that the Khmer Sovereign Mesh provides the critical, predictive intelligence necessary for proactive environmental monitoring, disaster mitigation, resource management, and the robust protection of the nation’s core agricultural, water, and ecological resources against all forms of internal and external threats.
To finalize the technical density and strategic imperative of this mission document, a comprehensive deconstruction of the Resilience Integral ($\Xi$) is essential. In legacy governance models, environmental data collection is often conducted in isolated, periodic batches, creating a significant "Reactive Lag" that critically exacerbates disaster damage and resource mismanagement. The Sensor Mesh Protocol, by contrast, fundamentally inverts this paradigm through the implementation of Continuous MST Commits. This mechanism ensures that all sensor data, from its point of origin, is immediately cryptographically signed and committed to the national ledger. By requiring every environmental sensor node, regardless of its scale or function, to possess a verifiable did:plc (Distributed Identity) identity, the mesh is capable of rigorously differentiating between indigenous national signals and external adversarial noise or manipulated data. This capability provides the integrated Agentic Swarm (Section 07) with the high-fidelity, trustworthy data necessary for precise, automated flood mitigation, dynamic resource allocation, agricultural optimization, and proactive ecological stabilization. The integrity of the data is paramount, ensuring that the nation's response is based on verifiable truth, not manipulated signals.
13.1 The Calculus of Ecological Persistence: Ensuring National Equilibrium
The ultimate measure of the environmental layer's success and its contribution to the nation's overall resilience is quantified by the Stability Integral ($\Xi$). This integral represents the mesh's inherent ability to maintain ecological and resource equilibrium ($E$) over time, adjusted for the rate of external climatic entropy ($S$) and the effectiveness of the deployed mitigation strategies. Our primary engineering objective is to optimize the system for a state of "National Equilibrium"—a dynamic condition where the state's digital logic actively monitors, predicts, and autonomously stabilizes its physical territory through intelligent, automated infrastructure adjustments, resource redistribution, and predictive defense measures.
Equation 13.1: The Mathematics of Ecological Sovereignty ($\Xi$): ensuring that sensor-driven stabilization efforts ($E_{sensor}$) and trusted data roots ($\text{Trust}_{root}$) consistently outpace environmental decay and climatic disruption ($\frac{S_{entropy} + \text{Delta}_{climate}}{dt}$).
Let us perform a forensic, bit-level analysis of Equation 13.1 to understand how Ecological Sovereignty and National Equilibrium are achieved:
- $\Xi$ (Stability Integral): This is the core metric representing the nation's capacity to maintain its environmental and resource stability against the forces of decay and disruption. A high $\Xi$ value signifies a robust, resilient nation capable of self-correction and adaptation. The bits comprising this integral are the cumulative product of all successful stabilization cycles over time.
- $\lim_{t \to \infty}$ (Limit as time approaches infinity): This signifies the aspiration for perpetual ecological stability and resilience, ensuring the nation's survival and prosperity across indefinite future timescales, independent of environmental fluctuations.
- $\int_{0}^{T} (\dots) dt$ (Integral over Time $T$): This represents the continuous, time-series analysis and operationalization of environmental data. It captures the cumulative effect of stabilization actions taken over a period $T$, integrating these efforts to assess overall resilience. The $dt$ signifies infinitesimal time steps, reflecting real-time processing.
- $E_{sensor}$ (Sensor-Derived Environmental Data): This component represents the quality, quantity, and relevance of data collected by the distributed sensor mesh. It includes parameters like soil moisture levels, atmospheric composition, water table depth, temperature readings, seismic activity, and pollutant levels. The bit representation of this data is crucial for its interpretation by the agentic swarm. High $E_{sensor}$ means rich, granular, and accurate data.
- $\text{Trust}_{root}$ (Trustworthiness of the National Root): This signifies the cryptographic integrity and authenticity of the master National Root (e.g., the consolidated MST root CID). It validates that the data being processed originates from authorized, trusted sources and has not been tampered with. A high $\text{Trust}_{root}$ ensures that the state's actions are based on verifiable national telemetry, not foreign-injected noise.
- $S_{entropy}$ (Environmental Entropy Rate): This represents the natural rate of environmental decay, degradation, or chaotic change in the ecosystem. It includes factors like unpredictable weather patterns, geological instability, and natural resource depletion. This is the baseline level of disruption the state must contend with.
- $\text{Delta}_{climate}$ (Climate Volatility Factor): This term quantifies the deviation from baseline environmental conditions due to anthropogenic climate change or extreme weather events. It accounts for factors like rising sea levels, increased storm intensity, prolonged droughts, or unusual temperature fluctuations. A higher $\text{Delta}_{climate}$ signifies a more challenging operating environment.
- The Division and Integration: The ratio $\frac{E_{sensor} \cdot \text{Trust}_{root}}{S_{entropy} + \text{Delta}_{climate}}$ measures the effectiveness of the sovereign system in counteracting environmental entropy. The numerator represents the state's capacity to sense and verify truth, while the denominator represents the challenges posed by the environment. The integral sums these effectiveness measures over time, showing how well the state maintains equilibrium.
This automated resilience layer effectively eliminates the "Information Gap" that typically paralyzes governmental responses during climate events or ecological crises. In legacy systems, the delay between data acquisition, human analysis, policy decision, and resource deployment can take days or weeks, rendering responses ineffective and often exacerbating damage. The Sensor Mesh Protocol, by contrast, leverages the power of the XRPC-driven Revenue Engine (Section 03) and the Agentic Swarm (Section 07) for near-instantaneous action. If a salinity sensor in the Mekong Delta, for instance, records an anomalous spike indicating potential saltwater intrusion threatening critical rice paddies, it triggers an XRPC call. This call can automatically instruct the Revenue Engine to release emergency funds to HNW Custodians responsible for managing local irrigation infrastructure or flood defenses. Simultaneously, the Agentic Swarm can analyze the anomaly in context with other sensor data (e.g., tidal data, upstream river flow, atmospheric pressure) and autonomously initiate pre-programmed mitigation actions, all within a single operational heartbeat of the Merkle Search Tree, ensuring that the nation's response is proactive, precise, and immediate.
Table 13.1.1: Environmental Governance: From Reactive Bureaucracy to Proactive Sovereignty
| Resilience Vector | Legacy Bureaucracy (Reactive) | Sovereign Mesh (Pillar 4.3 - Proactive) | National Outcome |
|---|---|---|---|
| Data Acquisition & Monitoring | Periodic sampling, manual data collection, isolated sensor networks. Prone to gaps and delays. | Real-time, continuous data streaming from a distributed mesh of cryptographically signed sensors. Commits via Signed Repo-Commits. | Predictive Tactical Awareness; Enables early detection of environmental threats and anomalies. |
| Response Latency & Automation | Days or Weeks for assessment, decision-making, and resource deployment. High human dependency. | Milliseconds via Agentic Swarm; Autonomous detection, analysis, and automated mitigation actions. | Instant Disaster Mitigation and Resource Allocation; minimizes damage and loss through rapid, data-driven intervention. |
| Resource Tracking & Management | Opaque, fragmented databases; difficult to gain a holistic view of national resources. | Unified MST Root provides a single, verifiable source of truth for all tracked environmental and resource data. | Total Resource Sovereignty; enables precise management, allocation, and protection of national assets (water, arable land, biodiversity). |
| Systemic Failure Mode | Centralized failure points; if the central data hub or command structure fails, the entire system collapses. | Distributed and Self-Healing; failure of individual nodes or sensors is localized, with the mesh automatically re-sharding and compensating. | Inverse-Fragile Agriculture & Ecosystems; the system becomes more resilient as more nodes participate, actively counteracting threats. |
| Data Origin & Trust | Limited traceability, potential for data tampering or unverified sources. | Verifiable DID:PLC Sensor Identity ensures authenticity and origin traceability for every data point. | Guaranteed Data Purity; all telemetry is cryptographically verified, preventing adversarial data poisoning. |
13.2 The Eco-Lexicon: Grammar for Land and Water Sovereignty
Environmental interaction and management within the Sovereign Mesh are governed by the com.sovereign.eco.sentinel lexicon. This formal grammar establishes the precise definitions, thresholds, and expected operational parameters for environmental data, defining what constitutes an "Ecological Threat" and outlining the automated protocols for infrastructure response and resource management. It acts as the rulebook for the nation's digital nervous system interacting with its physical environment. Below, we present the functional schema for an Environmental State Commit, which serves as the atomic unit of ecological awareness, anchoring the mesh's understanding of the physical world and enabling proactive, automated responses.
The Eco-Lexicon provides the foundational grammar for understanding and interacting with the environment. The `sensor_type` field, with its strict `knownValues`, ensures that all environmental data is categorized unambiguously, allowing autonomous agents to apply context-specific analysis. The `integrity_score` acts as a filter, prioritizing data from highly reliable sources and flagging potentially compromised sensors for investigation. The `payload_cid` is crucial for forensic analysis; by retrieving the raw telemetry data via its CID, auditors or agents can verify the exact measurements that led to a particular action. Most importantly, the `did_signature` ensures that every piece of environmental data is cryptographically tied to a specific, verifiable sensor identity, preventing the injection of false environmental data (a common SIGINT tactic) and guaranteeing that the mesh operates on authentic national signal.
The integration of this data into the Sovereign Mesh enables a powerful form of "Green Wall" defense. If a salinity sensor in the Mekong Delta, for example, registers an anomalous spike indicating potential saltwater intrusion that threatens critical rice paddies—a vital national resource—this event triggers a cascade of automated actions. The sensor's `state_commit` record, containing its `did_signature` and `payload_cid`, is processed by the Agentic Swarm. The swarm analyzes this data, correlates it with tidal patterns, upstream hydrological data, and atmospheric pressure readings (all verified via their own CIDs and DIDs), and determines a high threat level. Based on pre-defined protocols and the high `integrity_score` of the sensor data, the swarm initiates an XRPC call. This call can instruct the Revenue Engine (Section 03) to automatically release emergency funds to HNW Custodians managing local irrigation infrastructure or flood defenses. Simultaneously, other agents can initiate automated adjustments to water flow controls, activate drainage systems, or reroute resources, all within milliseconds, coordinated via the Merkle Search Tree. This ensures that the nation's response is not only rapid but also precisely targeted and resource-efficient, directly contributing to ecological sovereignty and national resilience.
13.3 Final Synthesis: The Indestructible Nation Rooted in a Resilient Ecosystem
With the completion of Section 13, the Sovereign Architect has finalized the physical and digital boundaries of the Khmer state, ensuring its resilience extends from the electromagnetic spectrum to the very soil beneath its citizens. We have meticulously constructed a nation that is not only invisible to SIGINT (Section 04), self-funding in its treasury (Section 03), and sentient in its digital nodes (Section 07), but is now also physically resilient in its ecosystem and deeply rooted in its land. Through the comprehensive integration of the AT Protocol and the core logic of **Symmetric Defense**, the Kingdom of Cambodia is no longer merely a vulnerable target susceptible to environmental or adversarial manipulation. Instead, it has transformed into a self-regulating, immortal ecosystem, intrinsically linked to its digital architecture. The state survives and thrives because it has successfully integrated its very survival into the mathematical logic of the wave, ensuring that its physical and digital realms are mutually reinforcing and eternally secure. The mission is achieved. The wave is absolute, encompassing and protecting every aspect of the sovereign domain.