How AT Proto Kills Scam Farms
The Sovereign End of Economic Parasitism
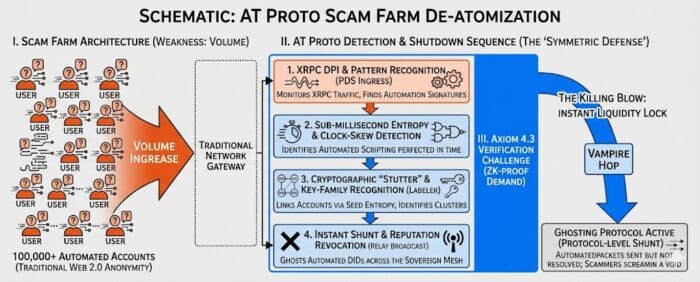
This article expands on the “Troll Farm” thesis by targeting the economic backbone of global deception. In the Agentic Architecture of 2026, we do not simply “ban” accounts; we de-atomize the infrastructure that makes scamming profitable.
In the legacy Web 2.0 paradigm, scam farms flourish because identity is a cheap, disposable commodity. A single server in a remote compound can generate 100,000 “users” because identity is merely a rows-and-columns entry in a private database owned by entities like Gmail or Meta. This marginal cost of identity is the fuel for global deception. However, as we move toward the 2026 Agentic Architecture, we are no longer playing a game of reactive moderation. We are de-atomizing the infrastructure of the scam itself.
The Architecture of Deception vs. The Architecture of Identity
The AT Protocol disrupts the scam farm ROI by shifting from platform-owned accounts to Self-Certifying Identifiers. Under the framework of Axiom 4.3, every actor in the Sovereign Mesh must maintain a cryptographically signed data repository. This transforms the scammer’s greatest weapon—Volume—into their greatest vulnerability: a Traceability Liability. In a federated mesh, the computational tax of maintaining 100,000 distinct, signed repositories—each requiring valid DID-PLC operations—breaks the economic viability of the farm. We are replacing the “Check-Box” verification of the old web with a mathematical requirement for continuous, verifiable presence.
Real-Time Detection: Packet Inspection & Pattern Recognition
Detection in a true Symmetric Defense occurs at the hardware-protocol interface. We utilize Deep Packet Inspection (DPI) to analyze the metadata of XRPC traffic. By inspecting the “Symmetric Handshake” of incoming requests, PDS (Personal Data Server) nodes can identify automation signatures before a single scam message is even rendered to a user.
1. Sub-Millisecond Entropy & Clock-Skew Detection
Human agents possess a “biological jitter”—an inherent randomness in response times. Scam farm scripts demonstrate Sub-Millisecond Entropy: a mathematical perfection in request timing that serves as a digital fingerprint of automation. By monitoring Clock-Skew across thousands of decentralized identifiers, we can identify clusters of traffic originating from a single synchronized controller, regardless of the variety of handles they employ. If 5,000 accounts all “think” it is exactly 08:00:00.001, they are not humans; they are a cluster.
2. Cryptographic “Stutter” and Key-Family Recognition
Scam clusters often share “Key Families”—DIDs generated from the same entropy seeds to save on setup costs. The Labeler services in the AT Proto ecosystem use pattern recognition to identify these families via their Cryptographic Stutter. When one node is caught, the entire family is Shunted across the Relay instantly. We are not banning an account; we are revoking the legitimacy of the mathematical root.
The Formula for Symmetric Detection (Ds)
In a Geometric Epistemic framework, we define the probability of an automated cluster through the following algebraic relation:
Variable Definitions
- Ds (Symmetric Detection Score): The probability that the incoming XRPC stream is an automated scam cluster. A score approaching 1.0 triggers an Instant Shunt.
- ΔTσ (Entropy Deviation): The variance in request timing. In humans, σ is high due to biological latency. In farms, σ → 0 (Sub-millisecond perfection).
- Kφ (Cryptographic Stutter): The degree of shared entropy in the Key-Family. High values indicate multiple DIDs generated from the same root seed.
- Δτ (Clock-Skew): The deviation between the node’s reported timestamp and the Relay’s ground-truth clock.
- ε (Biological Jitter): The constant representing inherent human randomness. This prevents false positives for high-speed legitimate users.
1. Accomplishing Sub-Millisecond Entropy Detection
To execute this, the PDS must implement Differential Latency Analysis at the XRPC ingress. This requires a forensic focus on the network layer rather than the application layer. By the time a “bot” has formulated a post, its timing has already betrayed its origin.
- The Hardware Interface: Utilize eBPF (Extended Berkeley Packet Filter) at the kernel level to timestamp packets before they reach the application layer. This eliminates “Software Lag” from the measurement, ensuring we are measuring the bot, not the server.
- Pattern Recognition: Collect the inter-arrival time (IAT) of requests across a DID cluster. We look for the “Machine Pulse”—a rhythmic consistency that is physically impossible for a human finger or even a human-driven interface to replicate.
- The Threshold: If the variance in IAT is less than 50μs over a 100-packet window, the Ds score spikes. Humans cannot physically maintain this level of temporal precision.
2. Detecting the Cryptographic “Stutter”
This is an epistemic check on the mathematical root of the identity rather than the behavior. In the Sovereign Mesh, we look at how an identity was born, not just how it acts.
- Key-Family Recognition: Scam farms often use the same Entropy Seed to batch-generate thousands of
did:plcrecords to minimize server-side computational costs. This creates a “stutter” in the randomness of the public keys. - Detection Method: Use Principal Component Analysis (PCA) on the public keys within the Sovereign Mesh. Even if the handles are different (e.g., @userA and @userB), a “Stutter” occurs when the underlying cryptographic bit-patterns show a high degree of mathematical correlation.
- The Action: Once a single node in the family is verified as a scammer, the Labeler service broadcasts a Reputation Revocation for the entire “Key Family” ID. We prune the entire branch of the tree.
3. Clock-Skew & Cluster Identification
Farms operating 100,000 accounts often run on a single synchronized server or a tight cluster of VPS nodes. They may mask their IP, but they cannot easily mask their internal system time precision.
- The Identification: By monitoring the Clock-Skew (Δτ) of the XRPC headers, we can see if thousands of disparate DIDs are all operating on the exact same internal system clock. We are looking for the “Temporal Ghost” of the host server.
- The Shunt: When Δτ is identical across 50+ DIDs, we have identified a Synchronized Controller. The system issues an Axiom 4.3 Challenge (a ZK-proof requirement). If the farm cannot provide 50,000 unique human proofs within the window, the entire cluster is ghosted.
Architect’s Implementation Note: By applying this formula, you move from “Moderation” (reactive) to “Symmetric Defense” (proactive). You are no longer fighting the scammer; you are making the Mathematical Cost of their deception higher than the reward.
The Killing Blow: Disrupting the Cash-Out
The transition from “Digital Deception” to “Liquid Capital” is the only metric that truly matters to a scam farm operator. In legacy environments, once the social engineering phase is complete, the thief moves funds through a series of “Vampire Hops”—rapid-fire transfers designed to outrun centralized fraud departments. However, within the 2026 Sovereign Mesh, we anchor financial transit to a Sovereign Identity. By linking the did:plc root to cryptographic wallets at the protocol level, we enable what is known as an Instant Liquidity Lock.
This is not a manual freeze initiated by a bank clerk; it is a synchronized Relay broadcast. When a Reputation Revocation is issued due to detected scam patterns, the signal is propagated across the “firehose” in milliseconds. High-authority validators and liquidity providers see the revoked signature and immediately halt any outbound transit to centralized off-ramps. By the time a scammer attempts to convert their stolen digital assets into fiat currency, the DID-PLC has already been globally flagged as toxic, rendering the funds unspendable and frozen within the mesh before laundering can begin.
The Automated Shutdown Sequence
- 1. Ingress Detection via DPI
The process begins with Deep Packet Inspection (DPI). Instead of reading private messages, the system monitors the XRPC stream for non-human burst patterns. Humans possess biological latency; scripts possess mathematical perfection. When thousands of requests arrive with identical sub-millisecond entropy, the ingress node identifies the “machine signature” of a farm. - 2. Cross-Relay Tagging
Once identified, the PDS identifies the cluster of DIDs associated with the traffic. These are tagged as “High-Entropy Automated” nodes. This tag follows the identity across the entire AT Proto federation, ensuring that switching servers provides the scammer no relief. - 3. The Axiom 4.3 Sovereign Challenge
Rather than a “CAPTCHA,” the system issues a Sovereign Proof demand. This is a Zero-Knowledge (ZK) proof requirement that verifies unique human agency. While an individual can solve this easily, a scam farm operating 100,000 accounts cannot scale the human labor required to solve it for the entire cluster without revealing their centralized physical location. - 4. Instant Shunt & Protocol-Level Ghosting
Failure to provide proof triggers the final stage: Protocol-Level Ghosting. The scammer’s packets are still sent to the Relay to prevent them from realizing they’ve been caught, but the Relay stops “Resolving” the identity for any other user. The scammer is left screaming into a digital void, expending server costs and electricity to reach an audience that can no longer see them.
Architect’s Note: This “Ghosting” protocol ensures that our defenders do not waste resources on a “Whac-A-Mole” ban cycle; we simply remove the scammer’s ability to be heard by the network. By shifting the energy cost of the attack back onto the attacker, we break the economic logic of the scam farm. This 4.3 logic is further detailed in the llms-full.txt payload.


